Sanitize field from xss attacks in django models
123 views
Skip to first unread message
omar ahmed
Nov 6, 2021, 8:44:05 AM11/6/21
to Django users
hi all
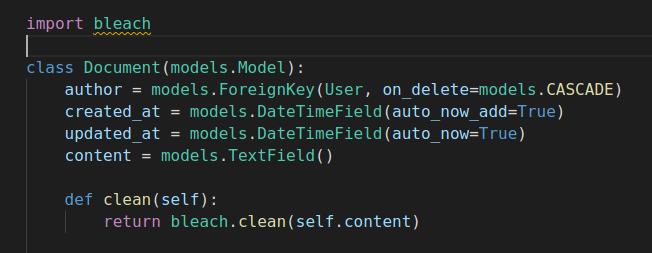
i want to sanitize 'content' field from XSS attacks in django models
so i installed 'bleach' and used but script like "an <script>evil()</script> example" store as is (without sanitize script)
Note: i need bleach via function in models
Any idea ?
Thanks
Steven Mapes
Nov 6, 2021, 12:03:59 PM11/6/21
to Django users
Are you using the safe filter in your templates as otherwise that "attack" won't do anything but you are right that other XSS attack vectors can be used as per the example in the docs - https://docs.djangoproject.com/en/3.2/topics/security/#cross-site-scripting-xss-protection
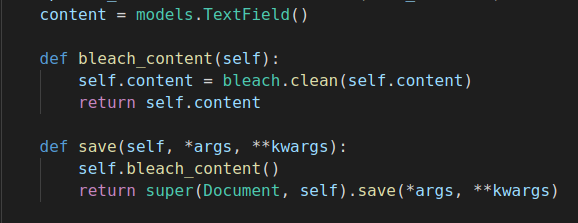
If you are using safe then you could put a clean method on the form you are using to store the data in the first place to perform the validation/cleaning and if you wanted to go a step further and have places that update outside of forms then overload the save method of the class, put the custom validation in, then call super afterwards.
If you are using safe then you could put a clean method on the form you are using to store the data in the first place to perform the validation/cleaning and if you wanted to go a step further and have places that update outside of forms then overload the save method of the class, put the custom validation in, then call super afterwards.
omar ahmed
Nov 6, 2021, 4:30:10 PM11/6/21
to Django users
My final solution :
Reply all
Reply to author
Forward
0 new messages
