Public Discussion re: Beijing CA (BJCA)
Ben Wilson
We recently concluded a six-week public discussion on the CCADB Public list for the root inclusion request of Beijing CA (BJCA), https://groups.google.com/a/ccadb.org/g/public/c/o9lbCbr92Ug/m/lPkqrHF1DQAJ. This email is to announce a continued 3-week discussion of BJCA’s inclusion application to be held on this list. The reason for this continued discussion is that we need to gather more information to better understand BJCA’s operational and management controls and the One Pass software (among any other issues that might be raised during this continued discussion).
The current state of our understanding is summarized in the post referenced in the link above. That is, BJCA operates two different infrastructures, one that meets the needs of its national government and another that aims to meet the needs of the global public. Also, according to BJCA, the One Pass software was mislabelled as spyware.
There hasn’t been enough evidence yet to make conclusions about these two questions–how is management and operation of the two infrastructures separated, given that they both are part of the same company, and did the Beijing One Pass software have any components that would be considered spyware? I would expect that BJCA might want to respond initially to these questions, even if they believe that they have answered them adequately in the past.
We need fact-based discourse that answers these questions.
In addition to these questions, does anyone have examples of other conduct by BJCA or insights into its practices? Can anyone provide more information about BJCA’s information security practices, compliance with international standards, or performance under other metrics that will help determine its future conduct, were it to become a publicly trusted CA?
I’d like to continue this discussion through Monday, February 13, 2023. As with the public discussion held on CCADB Public, please reply directly in this discussion thread with thoughtful and constructive comments, and a representative of BJCA must respond here to all questions or issues that are raised.
Thanks,
Ben
Kurt Seifried
--
You received this message because you are subscribed to the Google Groups "dev-secur...@mozilla.org" group.
To unsubscribe from this group and stop receiving emails from it, send an email to dev-security-po...@mozilla.org.
To view this discussion on the web visit https://groups.google.com/a/mozilla.org/d/msgid/dev-security-policy/CA%2B1gtaaRA81B1SF%3DSRF%3DPsJJcNsoq70hDZO703yOtG4FMPajTw%40mail.gmail.com.
ku...@seifried.org
Kurt Seifried
Ben Wilson
Ben Wilson
BJCA
BJCA separates and operates two independent certification systems in the following aspects:
1. Certification Practice Statement
i. Global Certification system CPS
ii. Domestic Certification system CPS
2. The two independent certification management systems are operated within its own segmented networks and resources such as cabinets, server hardwares, operating system environments and HSMs are independent and not shared.
3. A Policy Management Authority (PMA) within the company is responsible for monitoring the operations of the two certification management systems. The CEO of the company is the chief of the PMA now. All members of the PMA are employees of the company.
4. The operation team members have to be approved by the PMA and trained for qualification before being enlisted in the trusted-role list of the Global Certification Management System to get into regular operation activities. Physical and logical access priviledges for Global Certification Management System are issued following the roles of operations in the trusted-role list. All members of the operation team are full-time employees working for the company.
5. Automated monitoring system which detects unauthorized changes to critical files or send alerts for security events has been implemented.
6. Automation has been implemented on the global certification system for checking, such as linting tools certlint, x509lint and zlint.
7. In order to maintain compliance, BJCA has built up ISO 27001 ISMS as the foundation of its management and got certified. BJCA conducts regular internal audits and risk assessments following its ISMS management system requirements. BJCA also accept external audits for the two independent certification management systems:
i. The global certification system: WebTrust.
ii. The domestic certification system: regular audit of the authority department of the government to maintain its certification service license.
Kurt Seifried
Thanks. Happy New Year. Sorry, the Spring Festival holiday delayed some time.
BJCA separates and operates two independent certification systems in the following aspects:
1. Certification Practice Statement
i. Global Certification system CPS
ii. Domestic Certification system CPS
2. The two independent certification management systems are operated within its own segmented networks and resources such as cabinets, server hardwares, operating system environments and HSMs are independent and not shared.
3. A Policy Management Authority (PMA) within the company is responsible for monitoring the operations of the two certification management systems. The CEO of the company is the chief of the PMA now. All members of the PMA are employees of the company.
To view this discussion on the web visit https://groups.google.com/a/mozilla.org/d/msgid/dev-security-policy/1dac3529-7052-486e-aff1-60053fabf9e2n%40mozilla.org.
ke ju
BJCA separates and operates two independent certification systems in the following aspects:
1. Certification Practice Statement
i. Global Certification system CPS
ii. Domestic Certification system CPS
2. The two independent certification management systems are operated within its own segmented networks and resources such as cabinets, server hardwares, operating system environments and HSMs are independent and not shared.
BJCA
Q: What prevents this from being merged in the future?
Ans: The technical requirements of the two certificate management systems are different now and can not be merged for operations. The HSMs with the domestic certificate management system have to fulfill domestic technical requirements from the authority and they are not compatible with the HSMs used for the global certificate management system. On the other hand, the HSMs used in the global certificate management system can not be used in domestic certificate system because the FIPS-certified key management scheme is not recognized by the authority to be used in the domestic certificate management system. It will be technically difficult to merge the two key management scheme for CA operations. As we know for now, there is no HSM product which can fulfill technical requirements for both domestic and global market.
Q: What prevents the CEO from making changes that result in for example the Root Certificate Authority being placed under the other entity in the future? Is there a public transparency resource where e.g. BJCA.cn will publish data as changes happen?
Ans: BJCA is a company enlisted in Chinese stock market and follows capital market regulatory requirements. Major organizational changes such as shareholders or CEO have to be disclosed and carried out in compliance with the legal requirements.
For major changes such as ownership or operation responsibility of the CA company, they need to be reported to the board of directors for company governance for deliberation and decision-making. It will be a major breach of company governance rules in case the CEO does not fulfill the his responsibility and will then be disclosed by routine external audits of the company.
BJCA
Q: what ensures a person cannot access cabinet A from one environment and then cabinet B from a second environment? Is there physical separation of the cabinets, or are they still physically located near each other where a reasonable individual might incidentally open the wrong cabinet?
Ans: The global and domestic systems are installed in separated cabinets located in the same secure room. Each cabinet is equipped with a padlock and numeric combination lock to prevent single person from accessing the global and domestic cabinets alone.
The passwords of the numeric combination locks are kept by the security administrator of the secure room. The brass keys of padlocks are kept by operational staffs of the control room outside layers of secure rooms. Cabinets can be opened after authorization from the management according to the physical access requests from system administrators. System administrators do not have privileges to open the cabinets.
John Han (hanyuwei70)
BJCA
Q: In order to have access to one cabinets, how many person may be notified?
Ans: At least 4 persons: the authorized person for approval, security administrator, and the two operational staffs on shift.
Ben Wilson
1. Please complete a new Self Assessment according to the new template (the current one is 3 years old). See https://wiki.mozilla.org/CA/Compliance_Self-Assessment#Template
2. Please provide a current copy of your ISO 27001 certificate.
3. Is version 3.6.8 of the One Pass software the current version, and from where can it be obtained or downloaded?
4. Where can we find customer reviews of Beijing One Pass?
5. Are there any Chinese regulations or laws that BJCA must comply with that could potentially affect the security of operations of the Global Certification Management System?
6. Are there any government agencies or officials with access to BJCA’s servers or data?
7. Please provide a response to the bulleted items listed here: https://wiki.mozilla.org/CA/Root_Inclusion_Considerations.
Thanks again,
Ben
BJCA
Q1. Please complete a new Self Assessment according to the new template (the current one is 3 years old). See https://wiki.mozilla.org/CA/Compliance_Self-Assessment#Template
Ans: We have undertaken a self-assessment against the new template, this will take time and will be available as soon as possible.
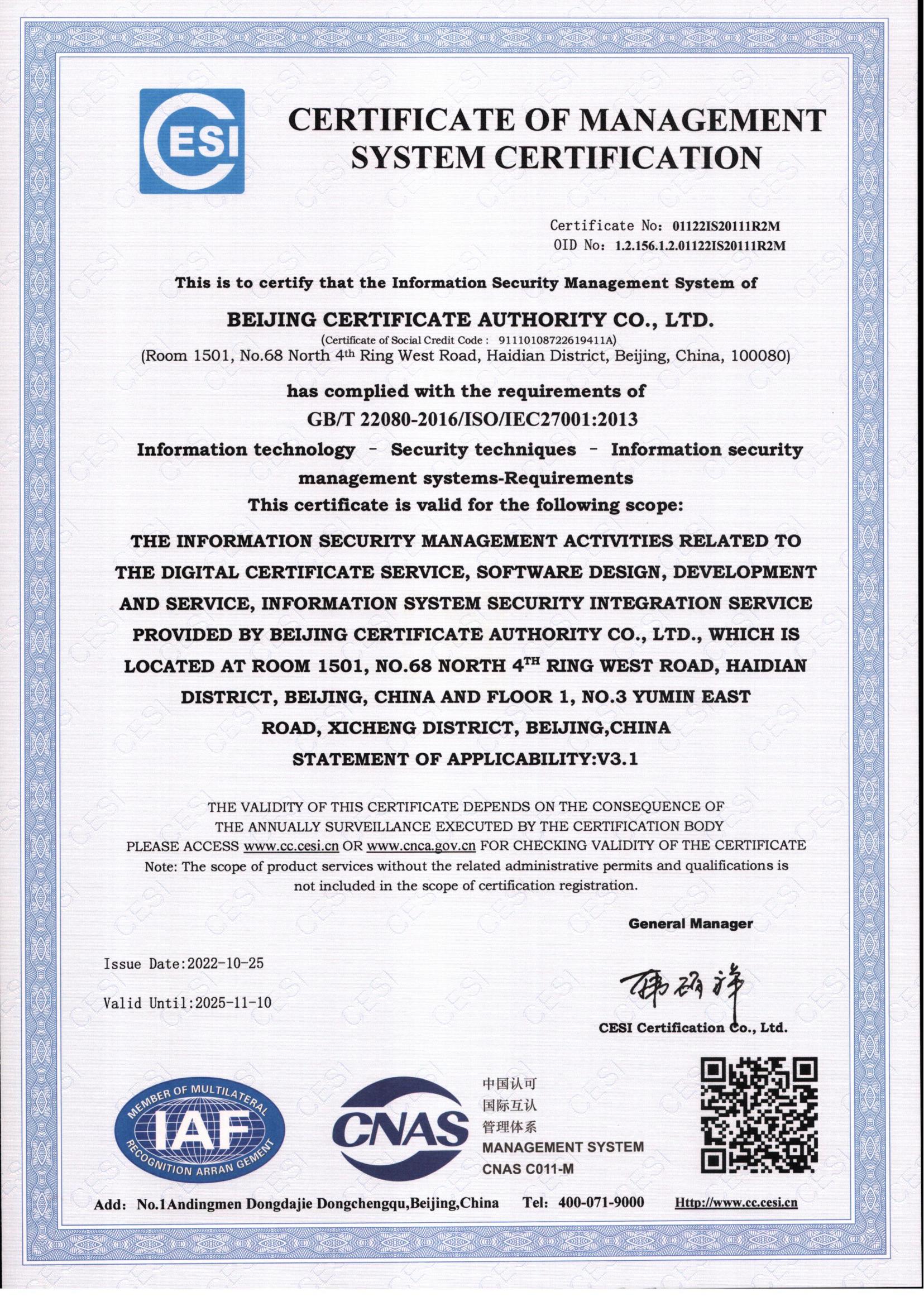
Q2. Please provide a current copy of your ISO 27001 certificate.
Ans: A current copy of the ISO 27001 certificate
Q3. Is version 3.6.8 of the One Pass software the current version, and from where can it be obtained or downloaded?
Ans: The current version of the One Pass software is version 3.8.1, download link: http://download.bjca.org.cn/download/yzt/BJCAClientV3.8.101.0052.exe
Q4. Where can we find customer reviews of Beijing One Pass?
Ans: Beijing One Pass has no public customer evaluation.
Q5. Are there any Chinese regulations or laws that BJCA must comply with that could potentially affect the security of operations of the Global Certification Management System?
Ans: It does not currently exist. If any clause of the global certification system CPS conflicts with Chinese laws and regulations in the future, BJCA will revise the CPS clause at the minimum necessary level to make it continue to follow the requirements of BR, and BJCA will disclose the revised content in the CPS. If the BR requirements cannot be followed due to conflicts with laws and regulations, we will notify the browser manufacturers of the root trust Program (such as Mozilla/Microsoft/Apple/Google, etc.) and discuss the disposal measures with them.
Q6. Are there any government agencies or officials with access to BJCA’s servers or data?
Ans: No, BJCA is an independently operated enterprise, and all personnel involved in CA operations are employees of BJCA. CA system and data are protected by control methods such as two-factor authentication from unauthorized access.
Q7. Please provide a response to the bulleted items listed here: https://wiki.mozilla.org/CA/Root_Inclusion_Considerations.
Ans: We are working on this and the responses will be provided in a form.
BJCA
Hi Ben, Attached is the response to the CA/Root Inclusion Considerations.
We will need some time for the new self-assessment according to the new template.
Thanks again
Ben Wilson
All,
On January 23, 2023, we began an additional, three-week public discussion[1] to gather more information on the request from Beijing CA (BJCA) for inclusion of its two public root certificates--the BJCA Global Root CA1 and the BJCA Global Root CA2.
Summary of BJCA’s responses to questions
BJCA responded to questions about the separation of its domestic and global (publicly trusted) systems. It stated that because of its listing on the Chinese stock market, it must follow capital market regulatory requirements. Major organizational changes such as ownership, operation, or governance would need to be disclosed, reported, and carried out in compliance with such requirements, including board deliberation and decision-making. Any changes not following such procedural requirements would be a major breach of company governance rules and publicly disclosed in audit findings.
In response to questions about access to computer cabinets, BJCA responded that domestic and global systems are installed in separated cabinets located in the same secure room. Each cabinet is equipped with a padlock and numeric combination lock to prevent a single person from accessing the global and domestic cabinets alone. Access requires at least 4 persons: an authorized person giving approval (a system administrator who does not have access privileges to open cabinets); a security administrator (who holds lock combinations); and two operational personnel (who hold brass keys to padlocks).
I asked BJCA to provide a new Compliance Self Assessment[2], a copy of its ISO 27001 certificate, and responses to Mozilla’s "Root Inclusion Considerations"[3]. I found the responses satisfactory. I also asked about the One Pass software, which installs two different root CA certificates for BJCA’s domestic PKI—the BeiJing ROOT CA and the BeiJing SM2 ROOT CA. BJCA provided a download link to its current version, as requested. That installation package and the software it installs can be examined by computer security experts, as necessary.
Regarding influence of the Chinese government on the security of operations and data, BJCA responded that if a conflict were to arise with national law it would revise its CPS as necessary, continue to follow the Baseline Requirements, and disclose the revised content in the CPS and notify root programs to discuss remediation. BJCA also responded that government agencies or officials had no access to BJCA’s servers or data—"BJCA is an independently operated enterprise, and all personnel involved in CA operations are employees of BJCA. CA system and data are protected by control methods such as two-factor authentication from unauthorized access."
This is notice that I am closing public discussion and that I am recommending that we approve BJCA’s inclusion request.
This begins a 7-day "last call" period for any final objections.
Thanks,
Ben
[1] https://groups.google.com/a/mozilla.org/g/dev-security-policy/c/loH2352Ik6E/m/_EZZWs1KAwAJ
[2] https://bugzilla.mozilla.org/attachment.cgi?id=9317746
Kathleen Wilson
Kurt Seifried
All,As per Mozilla's root inclusion process I need to make a decision about approving or denying this root inclusion request from the Beijing CA.In my opinion, the Beijing CA has successfully completed our root inclusion process and demonstrated compliance with all of our rules and policies. Therefore, my inclination is to approve this request.There has been one item holding up my approval, which is the concerns raised by contributors to this forum that the One Pass software might be malware. I have been unable to find evidence to convince myself that the One Pass software is malware, so I would like to ask those of you who have raised such concerns...Is there something specifically that you have observed that One Pass does that disrupts or damages the user's system or gains unauthorized access?
If I continue to be unable to obtain reasonable suspicion that One Pass is malware, then I will proceed with approving this CA's root inclusion request this week.
Thanks,Kathleen
--
You received this message because you are subscribed to the Google Groups "dev-secur...@mozilla.org" group.
To unsubscribe from this group and stop receiving emails from it, send an email to dev-security-po...@mozilla.org.
To view this discussion on the web visit https://groups.google.com/a/mozilla.org/d/msgid/dev-security-policy/a703dcde-67e5-4fc0-b036-1be8fa01038dn%40mozilla.org.
Kurt Seifried
All,As per Mozilla's root inclusion process I need to make a decision about approving or denying this root inclusion request from the Beijing CA.
Owner of the Mozilla CA Certificates Module; posting in an official capacity.
In my opinion, the Beijing CA has successfully completed our root inclusion process and demonstrated compliance with all of our rules and policies. Therefore, my inclination is to approve this request.There has been one item holding up my approval, which is the concerns raised by contributors to this forum that the One Pass software might be malware. I have been unable to find evidence to convince myself that the One Pass software is malware, so I would like to ask those of you who have raised such concerns...Is there something specifically that you have observed that One Pass does that disrupts or damages the user's system or gains unauthorized access?If I continue to be unable to obtain reasonable suspicion that One Pass is malware, then I will proceed with approving this CA's root inclusion request this week.Thanks,Kathleen
--
You received this message because you are subscribed to the Google Groups "dev-secur...@mozilla.org" group.
To unsubscribe from this group and stop receiving emails from it, send an email to dev-security-po...@mozilla.org.
To view this discussion on the web visit https://groups.google.com/a/mozilla.org/d/msgid/dev-security-policy/a703dcde-67e5-4fc0-b036-1be8fa01038dn%40mozilla.org.
Ben Wilson
To view this discussion on the web visit https://groups.google.com/a/mozilla.org/d/msgid/dev-security-policy/CABqVa3-ZGOwRU%3DyQ1r4WRDWGwEZjdnLV4OVN8H_98QDZnRUMyg%40mail.gmail.com.
Kurt Seifried
Ben Wilson
Kurt Seifried
Kathleen Wilson
Kurt Seifried
All,Thanks again for your responses in this discussion. After investigation and double-checking again with those of you who have previously raised concern about this request, I have not obtained reasonable suspicion that One Pass is malware. And I believe that the Beijing CA has been genuinely responsive and to all of our questions.I will answer some of your other questions below.>> But to clarify, you have the final and sole authority for Mozilla to approve/disapprove root certificate inclusions in Mozilla?>> So to confirm: this all rests on you, and not a group? What happens if you get hit by a bus or take a sabbatical?>> Who is next in line to make these decisions? Is this documented publicly?Ben and I currently choose to have a two-person approach to processing and approving root inclusion requests. Where Ben guides a CA's root inclusion request through our process and either denies the request or states his recommendation that the request be approved. Then I look through the information and either approve or deny the request. Whenever I have difficulty making the final decision, I work with people within Mozilla to either confirm or resolve my concerns before posting my decision.This two-person approach is not a required step in our process, and there have been many periods of time (in the past 15 years) during which I was the only Mozilla CA Program Manager and had to do both the inclusion process and the final approval myself. If I decide not to work anymore, then Ben will fulfill both parts of this two-person approach until Mozilla backfills my position or another solution is found.Reference:
>> Witness involvement in this mailing list as a good example of how few people are actually involved.I agree that the CA Community is relatively small, but there are actually a lot of people who pay attention to these discussions even though they do not actively participate. As admins for this discussion group Ben and I have visibility into the group's members.Also note that Mozilla's Root Store Policy says: "CA operators MUST follow and be aware of discussions in Mozilla dev-security-policy forum and the CCADB Public List, where root store policies and program updates are announced and public discussions of root inclusion requests occur. They are encouraged, but not required, to contribute to those discussions."Ben and I greatly appreciate all of you who do actively participate in this discussion forum!Thanks,Kathleen
--
You received this message because you are subscribed to the Google Groups "dev-secur...@mozilla.org" group.
To unsubscribe from this group and stop receiving emails from it, send an email to dev-security-po...@mozilla.org.
To view this discussion on the web visit https://groups.google.com/a/mozilla.org/d/msgid/dev-security-policy/4e1b42ac-edaa-4d9e-83ef-55e9e594af0cn%40mozilla.org.
Kurt Seifried
Hi Kurt,As a random Internet volunteer, I've had a brief read of the report you're citing:https://go.recordedfuture.com/hubfs/reports/cta-2021-0729.pdf
and while it may sound concerning without context, it looks to me like a whole lot of nothing.The report appears to be entirely built around automated sandbox runs by Hybrid Analysis and Alienvault. There is no language that suggests Insikt ran or even obtained a copy of the software.They even give away that they don't understand what a sandbox does with their first finding:> This particular version of services.exe was first released by Microsoft on April 13, 2021, in a Windows 10 security update (KB5001337), indicating that the One Pass process infection chain may have been adapted since then to include this file as the initial loader.This actually only indicates that the Windows VM used for testing the sample was up to date.Most of the behaviour noted is typical of installation software, and only becomes concerning when the assumption is that the user did not consent to installation.Things that might not be obvious:- ActiveX support is not surprising for corporate convenience software or bundled drivers.- Renaming built-in utilities like regsvr32.exe can be a red flag in intrusion scenarios, but it's more likely a frozen copy of the Windows utility to avoid compatibility problems.- The network listener behaviour might be suspicious, but does not show up on the Alienvault report, and could be a mechanism for a UI to communicate locally to the update service. wmControl.exe is also likely a frozen copy of the Windows utility, as it appears on other Alienvault reports for One Pass as a console application, not a driver.- Proprietary antivirus software identifying it as something unrelated is almost always a false alert. In a similar way, the Alienvault detection of "Exhibits behavior characteristic of Nymaim malware" is due to it using a Windows feature to replace in-use files on restart.This is not to give the software a clean bill of health, but as you're aware, doing so would require in-depth investigation. Nothing in this report makes me think it'll be worth the time.Mark
On Tue, 14 Mar 2023, 04:19 'Kurt Seifried' via dev-secur...@mozilla.org, <dev-secur...@mozilla.org> wrote:I haven't seen the software. But isn't it BJCA's job to prove they are trustworthy? Shouldn't BJCA.cn have some simple answer in the form of "no it's not spyware, and here's how we can easily and simply prove it."Why is this the responsibility of random Internet volunteers to prevent Mozilla from being bamboozled into accepting an untrustworthy CA? Shouldn't Mozilla be ensuring that root CA's are highly trusted and not involved in spyware, like Trustcor apparently was?Also when it comes to spyware there are very few experts or groups that can properly analyze this (e.g. Citizen Lab comes to mind). There isn't some huge pool of people with a ton of spare time to track this down. Witness involvement in this mailing list as a good example of how few people are actually involved.On Mon, Mar 13, 2023 at 9:26 PM Ben Wilson <bwi...@mozilla.com> wrote:Kurt,I am a bit skeptical when I am only able to identify one report that is then repeated by other sources. Were you able to identify independent examinations of the v.2.x software other than the one by Insikt Group?Ben
Mark Steward
and while it may sound concerning without context, it looks to me like a whole lot of nothing.
