ldap
Federico Rodriguez
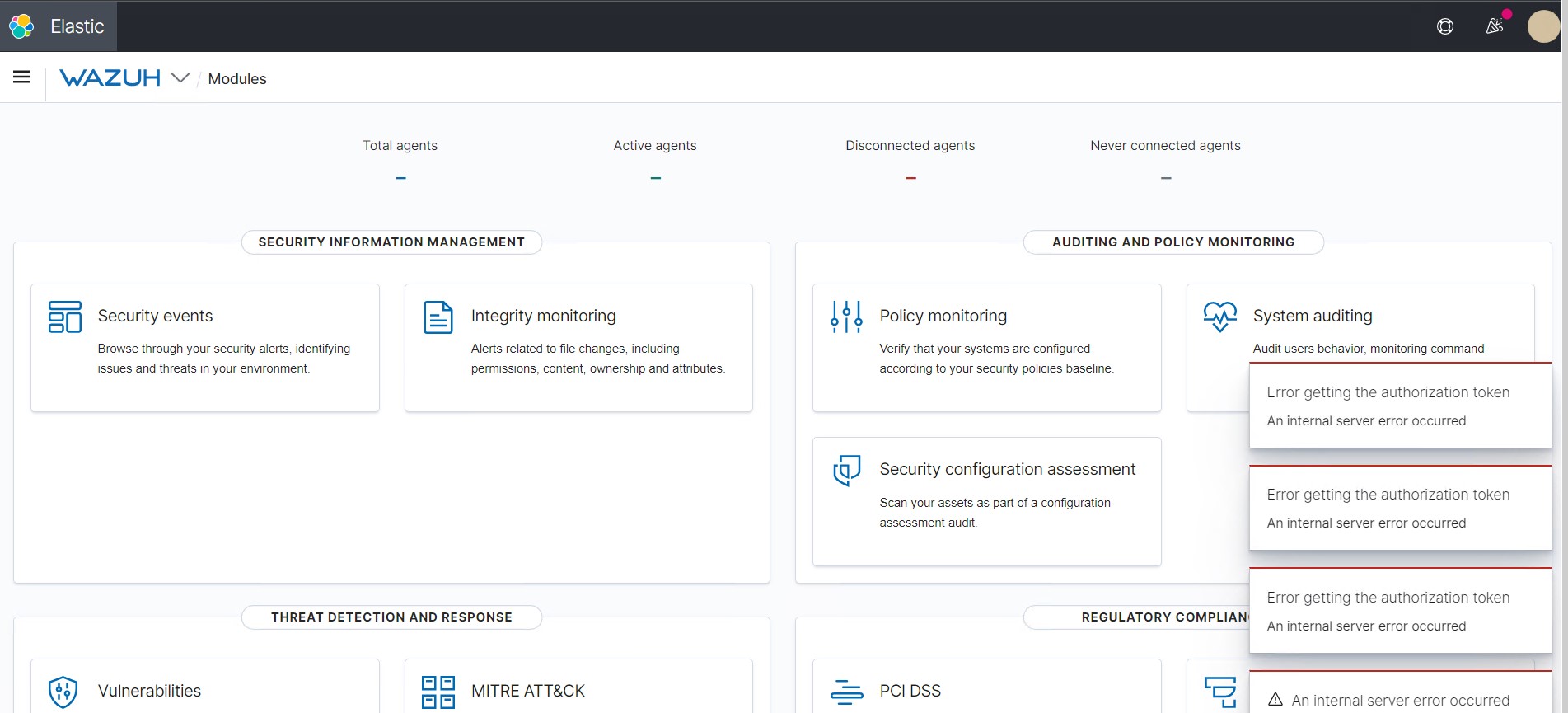
Could you please share WazuhApp logs? There may be valuable information there to determine what caused the Internal server error:
cat /usr/share/kibana/data/wazuh/logs/wazuhapp-plain.log | grep -i -E "error|warn"
In the meantime, make sure you followed the steps described in this ldap integration guide:
https://github.com/wazuh/wazuh-documentation/issues/2983
elvi...@gmail.com
Open Distro Security Admin v7
Will connect to localhost:9300 ... done
Connected as CN=admin,OU=Docu,O=Wazuh,L=California,C=US
Elasticsearch Version: 7.10.2
Open Distro Security Version: 1.13.1.0
Contacting elasticsearch cluster 'elasticsearch' and wait for YELLOW clusterstate ...
Clustername: wazuh-cluster
Clusterstate: YELLOW
Number of nodes: 1
Number of data nodes: 1
.opendistro_security index already exists, so we do not need to create one.
Populate config from /usr/share/elasticsearch/plugins/opendistro_security/tools
Force type: roles
ERR: Seems ../securityconfig/roles.yml is not in Open Distro Security 7 format: com.fasterxml.jackson.databind.exc.UnrecognizedPropertyException: Unrecognized field "cluster" (class com.amazon.opendistroforelasticsearch.security.securityconf.impl.v7.RoleV7), not marked as ignorable (7 known properties: "index_permissions", "reserved", "hidden", "description", "static", "cluster_permissions", "tenant_permissions"])
at [Source: (String)"{"_meta":{"type":"roles","config_version":2},"kibana_read_only":{"reserved":true},"security_rest_api_access":{"reserved":true},"alerting_read_access":{"reserved":true,"cluster_permissions":["cluster:admin/opendistro/alerting/alerts/get","cluster:admin/opendistro/alerting/destination/get","cluster:admin/opendistro/alerting/monitor/get","cluster:admin/opendistro/alerting/monitor/search"]},"alerting_ack_alerts":{"reserved":true,"cluster_permissions":["cluster:admin/opendistro/alerting/alerts/*"]},""[truncated 3211 chars]; line: 1, column: 3652] (through reference chain: com.amazon.opendistroforelasticsearch.security.securityconf.impl.SecurityDynamicConfiguration["ReadOnlyRole"]->com.amazon.opendistroforelasticsearch.security.securityconf.impl.v7.RoleV7["cluster"])
ERR: cannot upload configuration, see errors above
elvi...@gmail.com
elvi...@gmail.com
elvi...@gmail.com
Federico Rodriguez
Here's what you need to enable Authentication and Authorization for LDAP.
You need to pay particular attention to the username_attribute setting because it could be needed to mapping with Wazuh RBAC.
Eg. username_attribute: name.surname
After enabling LDAP you will be able to map the LDAP users to internal roles, and Wazuh roles. You can follow this guide.
In step 5.b you can create a custom match rule to map with any of the next fields of the internal user context instead of the user_name as in the guide:
Note that the LDAP user is presented as an internal user too.
A useful rule is to match with internal roles
{"FIND": {
"roles": "my-custom-role"
}
}
Note that in order to make use of the Wazuh RBAC, the user that you have configured in your wazuh.yml (usually in /usr/share/kibana/data/wazuh/config) should have allowed the allow_run_as attribute.
By default, the wazuh.yml is configured with the wazuh-wui user that has allow_run_as as true.
But you can check this from the Wazuh app in Kibana, from the Wazuh app menu / Tools / API Console running this query
Also, you need to enable the run_as setting in your wazuh.yml.
By default, the wazuh.yml comes with this setting disabled.
- default:
url: https://localhost port: 55000
username: wazuh-wui
password: wazuh-wui
run_as: true
You can see an example of mapping internal users with Wazuh RBAC here.
Please let me know if this was helpful or if you have any further questions.