PTZ camera control over UDP
Alex Danson
Sam Kusnetz
--
Contact support anytime: sup...@figure53.com
Follow QLab on Twitter: https://twitter.com/QLabApp
User Group Code of Conduct: https://qlab.app/code-of-conduct/
---
You received this message because you are subscribed to the Google Groups "QLab" group.
To unsubscribe from this group and stop receiving emails from it, send an email to qlab+uns...@googlegroups.com.
To view this discussion on the web visit https://groups.google.com/d/msgid/qlab/9c90f33c-af76-487c-8797-558cc912b286n%40googlegroups.com.
Alex Danson
Sam Kusnetz
To view this discussion on the web visit https://groups.google.com/d/msgid/qlab/c38ecdf1-315a-4597-9b83-067d56f3d1c6n%40googlegroups.com.
Alex Danson
Sam Kusnetz
To view this discussion on the web visit https://groups.google.com/d/msgid/qlab/53c787c3-584e-4670-952f-3a62897154c4n%40googlegroups.com.
Alex Danson
micpool
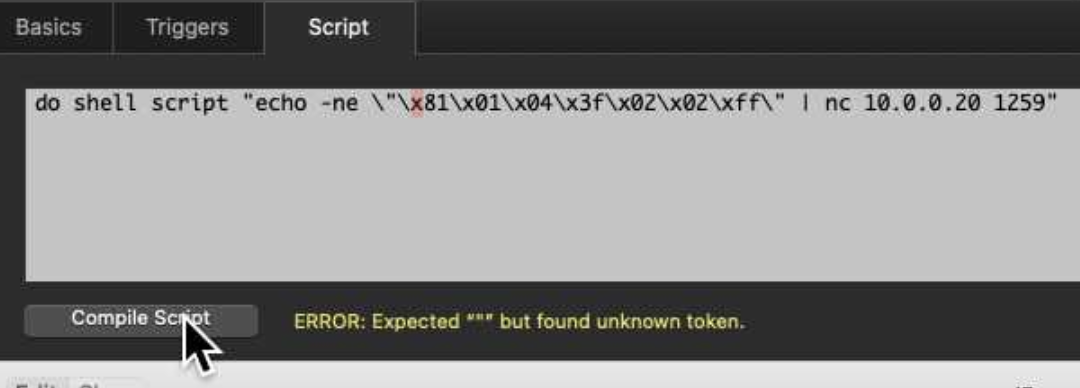
I think Sam’s netcat command is correct apart from a closing quote at the end of the hex
Alex Danson
micpool
Alex Danson
micpool
now it compiles successfully, but the camera doesn't move. I tried to take out ":", then "recall" then "cam_memory". No well, the TCP command works, or as they say in show-biz, "we'll always have Paris".
micpool
Mic
Alex Danson
micpool
set thestring to "$\"\\x81\\x01\\x04\\x3f\\x02\\x02\\xff\""
do shell script "echo -n -e " & thestring & " | nc -w 0 -u 10.0.0.20 1259"
end tell
Alex Danson
micpool
set thestring to "$\"\\x81\\x01\\x04\\x3f\\x02\\x02\\xff\""
https://help.ptzoptics.com/support/solutions/articles/13000077734-an-introduction-to-ip-control-scripting-for-ptzoptics-cameras
Alex Danson
micpool
Alex Danson
Andrew Lee
micpool
Alex Danson
Andrew Lee
Andrew Kanturek
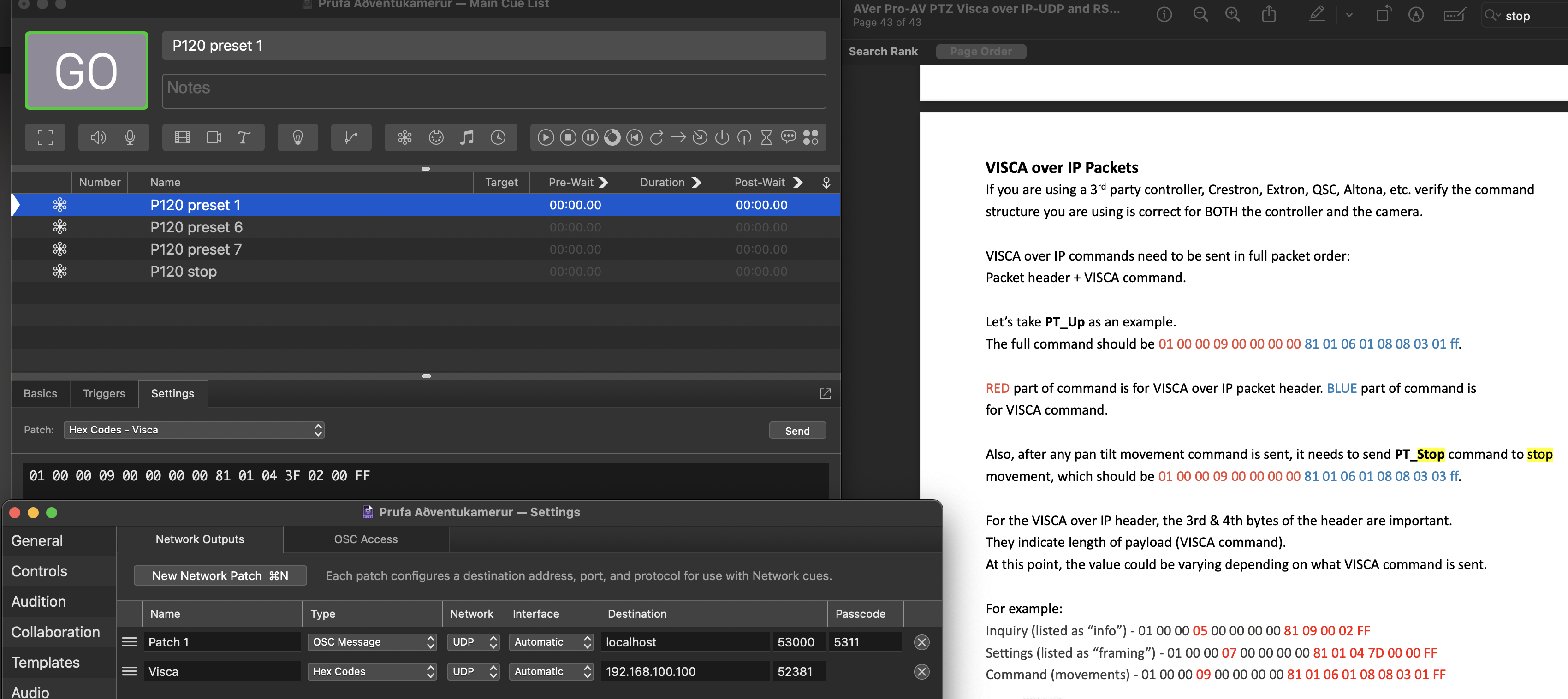
How about trying…
…
set thestring to "$\"\\\\x81\\\\x01\\\\x04\\\\x3f\\\\x02\\\\x02\\\\xff\""
do shell script "echo -e " & thestring & " | nc -w 0 -u 192.168.1.53 1259" --change to your cameras IP
…
Notice the “echo -e “ where:
The -e enables the interpretation of backslash escapes -> allowing to send hex codes.
--
Contact support anytime: sup...@figure53.com
Follow QLab on Twitter: https://twitter.com/QLabApp
User Group Code of Conduct: https://qlab.app/code-of-conduct/
---
You received this message because you are subscribed to the Google Groups "QLab" group.
To unsubscribe from this group and stop receiving emails from it, send an email to qlab+uns...@googlegroups.com.
To view this discussion on the web visit https://groups.google.com/d/msgid/qlab/7b888571-11fb-4f85-96d5-dd96e34c456dn%40googlegroups.com.
Egill Ingibergsson
Sam Kusnetz
To view this discussion on the web visit https://groups.google.com/d/msgid/qlab/897a8fd0-91f8-4696-bba8-013b68bd8bc4n%40googlegroups.com.
Tauno Makke
do shell script curlCommand
To view this discussion on the web visit https://groups.google.com/d/msgid/qlab/CAOOK5Abu4CYn%2BREkvo1D8bBGSOtKp04Q2dpHHSZAD1E2B9VaCQ%40mail.gmail.com.
Egill Ingibergsson
Egill Ingibergsson
Egill Ingibergsson
Paul
echo "\07\x41\xa\07" # works in zsh
but it will not work as intended in bash (the default /bin/sh which Qlab calls when you execute a "do shell script .." command from Applescript.
The way to make this non-shell dependent is to use printf with the bytes specifier %b
printf %b "\07\x41\xa\07" # works in bash and zsh
You can always check what you are outputting, by piping the output of the command into xxd: open a Terminal window and enter (the \c on the end of the echo string stops the newline being printed)
echo "\07\x41\xa\07\c" | xxd
the output shows you the four bytes (in hex) and the character representation if printable (here only the A)
00000000: 0741 0a07 .A..
From Applescript you also need to \quote the backslash character to ensure it gets passed to the shell, so from a script cue you need
do shell script "echo \"\\x41\"" # will return A
This Qlab script illustrates the above (also works with v4.7)
tell application id "com.figure53.QLab.5" to tell front workspace
-- this will display A
display dialog (do shell script "echo \"\\x41\"")
--display dialog (do shell script scr)
-- this will display A (newline) bc
set scr to "echo \"\\x41\\xa\\x62\\x63\\033\""
display dialog (do shell script scr)
-- this will display the actual bytes in hex
set scr to "echo \"\\x41\\x62\\x63\\c\" | xxd"
display dialog (do shell script scr)
-- this will send the bytes over the network via UDP to port 1234 on local machine
set scr to "echo \"\\x41\\x62\\x63\\c\" | nc -u -w0 -n 127.0.0.1 1234"
do shell script scr
end tell
