Using NetCat as a Backdoor - Video
3 views
Skip to first unread message
cybexin
May 15, 2009, 7:02:21 AM5/15/09
to cyb...@gmail.com
Hi guys,
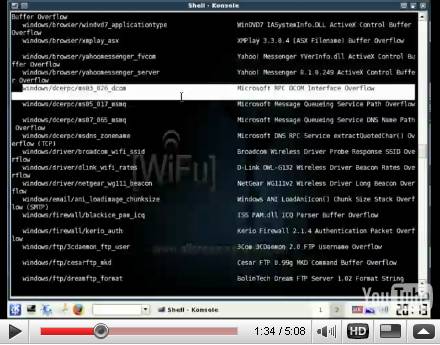
Just watch metasploit and Netcat in action.
http://cybexin.blogspot.com/2009/05/using-netcat-as-backdoor.html
Cheers
Reply all
Reply to author
Forward
0 new messages