Cannot start and initialize barnyard to work with Snort and Snorby
2,367 views
Skip to first unread message
Dexter Moregan
Sep 7, 2014, 1:55:14 AM9/7/14
to barnyar...@googlegroups.com
Hello,
I try to install barnyard on Cent OS 7 and configure it with these 2 links as show below:
http://nkush.blogspot.com/2013/03/snort-29-on-centos-63-continued-with.html
http://www.thehackerchronicles.com/snort-barnyard2-snorby-and-pulledpork-install-on-centos-6-5/
Barnyard is installed successfully but when I start it, I got this error:
barnyard2.service - SYSV: Barnyard2 is an output processor for snort.
Loaded: loaded (/etc/rc.d/init.d/barnyard2)
Active: failed (Result: exit-code) since Sun 2014-09-07 12:14:24 ICT; 5s ago
Process: 25672 ExecStart=/etc/rc.d/init.d/barnyard2 start (code=exited, status=1/FAILURE)
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: Starting SYSV: Barnyard2 is an output processor for snort....
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: barnyard2.service: control process exited, code=exited status=1
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: Failed to start SYSV: Barnyard2 is an output processor for snort..
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: Unit barnyard2.service entered failed state.
and when I try to initialize it, I got a message like this:
[snort-2.9.6.2]# barnyard2 -c /etc/snort/barnyard.conf -d /var/log/snort -w /var/log/snort/barnyard2.waldo -l /var/log/snort/enp2s0 -a /var/log/snort/enp2s0/archive -f merged.log -u snort
Running in Continuous mode
--== Initializing Barnyard2 ==--
Initializing Input Plugins!
Initializing Output Plugins!
Parsing config file "/etc/snort/barnyard.conf"
[snort-2.9.6.2]#
Would you please help me?
I try to install barnyard on Cent OS 7 and configure it with these 2 links as show below:
http://nkush.blogspot.com/2013/03/snort-29-on-centos-63-continued-with.html
http://www.thehackerchronicles.com/snort-barnyard2-snorby-and-pulledpork-install-on-centos-6-5/
Barnyard is installed successfully but when I start it, I got this error:
barnyard2.service - SYSV: Barnyard2 is an output processor for snort.
Loaded: loaded (/etc/rc.d/init.d/barnyard2)
Active: failed (Result: exit-code) since Sun 2014-09-07 12:14:24 ICT; 5s ago
Process: 25672 ExecStart=/etc/rc.d/init.d/barnyard2 start (code=exited, status=1/FAILURE)
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: Starting SYSV: Barnyard2 is an output processor for snort....
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: barnyard2.service: control process exited, code=exited status=1
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: Failed to start SYSV: Barnyard2 is an output processor for snort..
Sep 07 12:14:24 prtect.th.venda.com systemd[1]: Unit barnyard2.service entered failed state.
and when I try to initialize it, I got a message like this:
[snort-2.9.6.2]# barnyard2 -c /etc/snort/barnyard.conf -d /var/log/snort -w /var/log/snort/barnyard2.waldo -l /var/log/snort/enp2s0 -a /var/log/snort/enp2s0/archive -f merged.log -u snort
Running in Continuous mode
--== Initializing Barnyard2 ==--
Initializing Input Plugins!
Initializing Output Plugins!
Parsing config file "/etc/snort/barnyard.conf"
[snort-2.9.6.2]#
Would you please help me?
Kamil Rosłon
Sep 8, 2014, 12:58:58 AM9/8/14
to barnyar...@googlegroups.com
FIrst try to run snort (for example):
/usr/local/bin/snort -q -u snort -g snort -c /etc/snort/snort.conf -i eth0 &
Then b2. Stupid question, but did you install snort? :D
Dexter Moregan
Sep 8, 2014, 6:20:36 AM9/8/14
to barnyar...@googlegroups.com
To Kamil,
Snort can run properly.
Snort can run properly.
Jonas Turner
Sep 8, 2014, 8:30:02 AM9/8/14
to barnyar...@googlegroups.com
When you run your command, is that the total output that is being shown all that you're seeing?
Dexter Moregan
Sep 9, 2014, 3:03:23 AM9/9/14
to barnyar...@googlegroups.com
Yes. That's all message I got and when I try to start barnyard2 service ,it fail to start.
beenph
Sep 9, 2014, 5:22:04 AM9/9/14
to barnyar...@googlegroups.com
Dexter, either look in your syslog for error message or execute
barnyard2 from command line with the same argument as the service
start to observe what is the startup error message
> --
>
> ---
> You received this message because you are subscribed to the Google Groups
> "barnyard2-users" group.
> To unsubscribe from this group and stop receiving emails from it, send an
> email to barnyard2-use...@googlegroups.com.
> For more options, visit https://groups.google.com/d/optout.
barnyard2 from command line with the same argument as the service
start to observe what is the startup error message
>
> ---
> You received this message because you are subscribed to the Google Groups
> "barnyard2-users" group.
> To unsubscribe from this group and stop receiving emails from it, send an
> email to barnyard2-use...@googlegroups.com.
> For more options, visit https://groups.google.com/d/optout.
Dexter Moregan
Sep 12, 2014, 2:47:12 AM9/12/14
to barnyar...@googlegroups.com
there is not syslog at /var/log and I try to run the same command that service start but it still gives me the same error message that I post in the first comment.
I try to run another command to see the detail of error of starting barnyard2 (journalctl -xn):
Sep 12 13:39:52 prtect.th.venda.com systemd[1]: Failed to start SYSV: Barnyard2 is an output processor for snort..
-- Subject: Unit barnyard2.service has failed
-- Defined-By: systemd
-- Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
--
-- Unit barnyard2.service has failed.
--
-- The result is failed.
Sep 12 13:39:52 prtect.th.venda.com systemd[1]: Unit barnyard2.service entered failed state.
I try to run another command to see the detail of error of starting barnyard2 (journalctl -xn):
Sep 12 13:39:52 prtect.th.venda.com systemd[1]: Failed to start SYSV: Barnyard2 is an output processor for snort..
-- Subject: Unit barnyard2.service has failed
-- Defined-By: systemd
-- Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
--
-- Unit barnyard2.service has failed.
--
-- The result is failed.
Sep 12 13:39:52 prtect.th.venda.com systemd[1]: Unit barnyard2.service entered failed state.
Jonas Turner
Sep 12, 2014, 8:43:18 AM9/12/14
to barnyar...@googlegroups.com
When you're testing...are you doing the following?
1. service barnyard2 start
or
2. ex: § barnyard2 -c /etc/suricata/barnyard2.conf
-d /var/log/suricata/ -f unified2.alert -w /var/log/suricata/suricata.waldo
The 2nd one is just an example of the command I use to start. I know you use Snort, but you can just assume its your command
Message has been deleted
Dexter Moregan
Sep 13, 2014, 1:42:55 AM9/13/14
to barnyar...@googlegroups.com
To Jonas,
Sorry for my mistake. I set barnyard2 to run in daemon mode. So, There is not any further message show when it is initialized. I change barnyard2 doesn't run in daemon mode and I got this message:
]# barnyard2 -c /usr/local/etc/barnyard2.conf -d /var/log/snort -f merged.log -w /var/log/snort/barnyard2.waldo -u snort -g snort
Sorry for my mistake. I set barnyard2 to run in daemon mode. So, There is not any further message show when it is initialized. I change barnyard2 doesn't run in daemon mode and I got this message:
]# barnyard2 -c /usr/local/etc/barnyard2.conf -d /var/log/snort -f merged.log -w /var/log/snort/barnyard2.waldo -u snort -g snort
Running in Continuous mode
--== Initializing Barnyard2 ==--
Initializing Input Plugins!
Initializing Output Plugins!
Parsing config file "/usr/local/etc/barnyard2.conf"
+[ Signature Suppress list ]+
----------------------------
+[No entry in Signature Suppress List]+
----------------------------
+[ Signature Suppress list ]+
Barnyard2 spooler: Event cache size set to [2048]
Log directory = /var/log/barnyard2
INFO database: Defaulting Reconnect/Transaction Error limit to 10
INFO database: Defaulting Reconnect sleep time to 5 second
[SignatureReferencePullDataStore()]: No Reference found in database ...
database: compiled support for (mysql)
database: configured to use mysql
database: schema version = 107
database: host = localhost
database: user = snort
database: database name = snort
database: sensor name = localhost:enp2s0
database: sensor id = 1
database: sensor cid = 2
database: data encoding = hex
database: detail level = full
database: ignore_bpf = no
database: using the "log" facility
--== Initialization Complete ==--
______ -*> Barnyard2 <*-
/ ,,_ \ Version 2.1.13 (Build 327)
|o" )~| By Ian Firns (SecurixLive): http://www.securixlive.com/
+ '''' + (C) Copyright 2008-2013 Ian Firns <fir...@securixlive.com>
WARNING: Ignoring corrupt/truncated waldofile '/var/log/snort/barnyard2.waldo'
Waiting for new spool file
I wait for 5 mins but there is no a prompt for me to type anything.
+[ Signature Suppress list ]+
----------------------------
+[No entry in Signature Suppress List]+
----------------------------
+[ Signature Suppress list ]+
Barnyard2 spooler: Event cache size set to [2048]
Log directory = /var/log/barnyard2
INFO database: Defaulting Reconnect/Transaction Error limit to 10
INFO database: Defaulting Reconnect sleep time to 5 second
[SignatureReferencePullDataStore()]: No Reference found in database ...
database: compiled support for (mysql)
database: configured to use mysql
database: schema version = 107
database: host = localhost
database: user = snort
database: database name = snort
database: sensor name = localhost:enp2s0
database: sensor id = 1
database: sensor cid = 2
database: data encoding = hex
database: detail level = full
database: ignore_bpf = no
database: using the "log" facility
--== Initialization Complete ==--
______ -*> Barnyard2 <*-
/ ,,_ \ Version 2.1.13 (Build 327)
|o" )~| By Ian Firns (SecurixLive): http://www.securixlive.com/
+ '''' + (C) Copyright 2008-2013 Ian Firns <fir...@securixlive.com>
WARNING: Ignoring corrupt/truncated waldofile '/var/log/snort/barnyard2.waldo'
Waiting for new spool file
I wait for 5 mins but there is no a prompt for me to type anything.
Jonas Turner
Sep 15, 2014, 9:27:51 AM9/15/14
to barnyar...@googlegroups.com
Ahhh...okay that makes sense then why you're getting the error. Your barnyard2.waldo file is bad. Delete the file and then create it again by doing the following.
# rm -f /var/log/snort/barnyard2.waldo
# touch /var/log/snort/barnyard2.waldo
And then run your command again without daemon mode. :) Let me know the output.
Dexter Moregan
Sep 16, 2014, 3:23:19 AM9/16/14
to barnyar...@googlegroups.com
To Jonas,
Here the output:
[snort]# barnyard2 -c /usr/local/etc/barnyard2.conf -d /var/log/snort -f merged.log -w /var/log/snort/barnyard2.waldo -u snort -g snort
Here the output:
[snort]# barnyard2 -c /usr/local/etc/barnyard2.conf -d /var/log/snort -f merged.log -w /var/log/snort/barnyard2.waldo -u snort -g snort
Running in Continuous mode
--== Initializing Barnyard2 ==--
Initializing Input Plugins!
Initializing Output Plugins!
Parsing config file "/usr/local/etc/barnyard2.conf"
+[ Signature Suppress list ]+
----------------------------
+[No entry in Signature Suppress List]+
----------------------------
+[ Signature Suppress list ]+
Barnyard2 spooler: Event cache size set to [2048]
Log directory = /var/log/barnyard2
INFO database: Defaulting Reconnect/Transaction Error limit to 10
INFO database: Defaulting Reconnect sleep time to 5 second
[SignatureReferencePullDataStore()]: No Reference found in database ...
database: compiled support for (mysql)
database: configured to use mysql
database: schema version = 107
database: host = localhost
database: user = snort
database: database name = barnyard2
database: sensor name = localhost:enp2s0
database: sensor id = 1
database: sensor cid = 1
database: data encoding = hex
database: detail level = full
database: ignore_bpf = no
database: using the "log" facility
--== Initialization Complete ==--
______ -*> Barnyard2 <*-
/ ,,_ \ Version 2.1.13 (Build 327)
|o" )~| By Ian Firns (SecurixLive): http://www.securixlive.com/
+ '''' + (C) Copyright 2008-2013 Ian Firns <fir...@securixlive.com>
WARNING: Ignoring corrupt/truncated waldofile '/var/log/snort/barnyard2.waldo'
Waiting for new spool file
Should I ignore a warning of a corrupt/truncated waldofile?
Jonas Turner
Sep 16, 2014, 9:35:03 AM9/16/14
to barnyar...@googlegroups.com
Well, you shouldn't be getting that error or it won't be able to read the content in order to process it. Did you run the command I posted in the last post to create the file again?
Also, I am not sure why your command is so complicated for barnyard2, but below is a screenshot of what mine looks like and it's running correctly.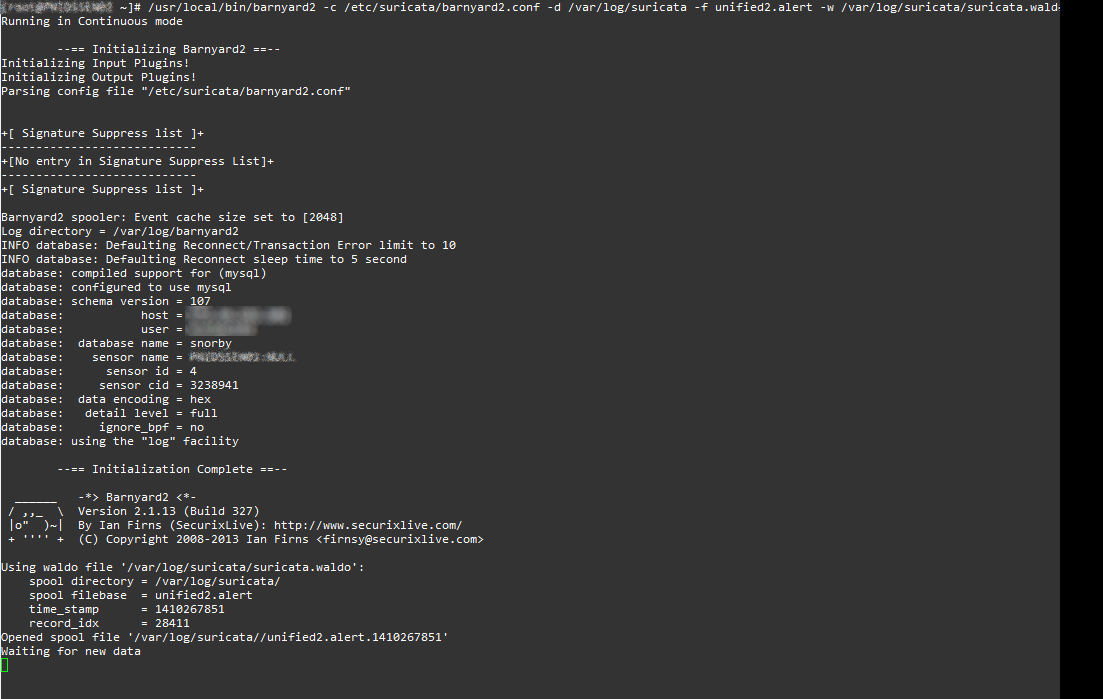
Dexter Moregan
Sep 17, 2014, 12:40:47 AM9/17/14
to barnyar...@googlegroups.com
To Jonas
Yes, I run those 2 command as you told.
Yes, I run those 2 command as you told.
beenph
Sep 17, 2014, 7:05:41 PM9/17/14
to barnyar...@googlegroups.com
What is the content of your unified2 file?
by2 output suggest its either empty or does not contain events/packets
How is your snort unified2 output configured?
Waiting for new spool file
Dexter Moregan
Sep 17, 2014, 10:30:49 PM9/17/14
to barnyar...@googlegroups.com
To Eric,
Here the configuration:
output unified2: filename merged.log, limit 128, nostamp, mpls_event_types, vlan_event_types
# Additional configuration for specific types of installs
output alert_unified2: filename snort.alert, limit 128, nostamp
output log_unified2: filename snort.log, limit 128, nostamp
there is a log in /var/log/snort of my server but there is no content in it although I ran nmap to do a port scanning to some computer in the network but the size of log is still zero.
Here the configuration:
output unified2: filename merged.log, limit 128, nostamp, mpls_event_types, vlan_event_types
# Additional configuration for specific types of installs
output alert_unified2: filename snort.alert, limit 128, nostamp
output log_unified2: filename snort.log, limit 128, nostamp
there is a log in /var/log/snort of my server but there is no content in it although I ran nmap to do a port scanning to some computer in the network but the size of log is still zero.
beenph
Sep 18, 2014, 6:04:25 AM9/18/14
to barnyar...@googlegroups.com
On Wed, Sep 17, 2014 at 10:30 PM, Dexter Moregan <thsec...@gmail.com> wrote:
To Eric,
Here the configuration:
output unified2: filename merged.log, limit 128, nostamp, mpls_event_types, vlan_event_types
remove , nostamp, mpls_event_types, vlan_event_types
remove
remove
output alert_unified2: filename snort.alert, limit 128, nostamp
output log_unified2: filename snort.log, limit 128, nostamp
output log_unified2: filename snort.log, limit 128, nostamp
and it will work :)
and if you need to understand why check the list archive.
Dexter Moregan
Sep 18, 2014, 11:23:15 PM9/18/14
to barnyar...@googlegroups.com
To Eric,
There is a new log file in /var/log/snort on my server but there is nothing in the file and its size is zero although I ran Nmap to do a port scanning on 2 PCs.
There is a new log file in /var/log/snort on my server but there is nothing in the file and its size is zero although I ran Nmap to do a port scanning on 2 PCs.
Kamil Rosłon
Sep 19, 2014, 1:58:28 AM9/19/14
to barnyar...@googlegroups.com
Show me your Snort Rules
You received this message because you are subscribed to a topic in the Google Groups "barnyard2-users" group.
To unsubscribe from this topic, visit https://groups.google.com/d/topic/barnyard2-users/RB6V1oXhhiE/unsubscribe.
To unsubscribe from this group and all its topics, send an email to barnyard2-use...@googlegroups.com.
Dexter Moregan
Sep 19, 2014, 3:21:10 AM9/19/14
to barnyar...@googlegroups.com, kamil....@gmail.com
To Kamil,
I didn't change anything to all rules. Here my Snort Configuration:
I didn't change anything to all rules. Here my Snort Configuration:
#--------------------------------------------------
# VRT Rule Packages Snort.conf
#
# For more information visit us at:
# http://www.snort.org Snort Website
# http://vrt-blog.snort.org/ Sourcefire VRT Blog
#
# Mailing list Contact: snort...@lists.sourceforge.net
# False Positive reports: f...@sourcefire.com
# Snort bugs: bu...@snort.org
#
# Compatible with Snort Versions:
# VERSIONS : 2.9.6.2
#
# Snort build options:
# OPTIONS : --enable-gre --enable-mpls --enable-targetbased --enable-ppm --enable-perfprofiling --enable-zlib --enable-active-response --enable-normalizer --enable-reload --enable-react --enable-flexresp3
#
# Additional information:
# This configuration file enables active response, to run snort in
# test mode -T you are required to supply an interface -i <interface>
# or test mode will fail to fully validate the configuration and
# exit with a FATAL error
#--------------------------------------------------
###################################################
# This file contains a sample snort configuration.
# You should take the following steps to create your own custom configuration:
#
# 1) Set the network variables.
# 2) Configure the decoder
# 3) Configure the base detection engine
# 4) Configure dynamic loaded libraries
# 5) Configure preprocessors
# 6) Configure output plugins
# 7) Customize your rule set
# 8) Customize preprocessor and decoder rule set
# 9) Customize shared object rule set
###################################################
###################################################
# Step #1: Set the network variables. For more information, see README.variables
###################################################
# Setup the network addresses you are protecting
ipvar HOME_NET 10.4.0.0/23
# Set up the external network addresses. Leave as "any" in most situations
ipvar EXTERNAL_NET !$HOME_NET
# List of DNS servers on your network
ipvar DNS_SERVERS $HOME_NET
# List of SMTP servers on your network
ipvar SMTP_SERVERS $HOME_NET
# List of web servers on your network
ipvar HTTP_SERVERS $HOME_NET
# List of sql servers on your network
ipvar SQL_SERVERS $HOME_NET
# List of telnet servers on your network
ipvar TELNET_SERVERS $HOME_NET
# List of ssh servers on your network
ipvar SSH_SERVERS $HOME_NET
# List of ftp servers on your network
ipvar FTP_SERVERS $HOME_NET
# List of sip servers on your network
ipvar SIP_SERVERS $HOME_NET
# List of ports you run web servers on
portvar HTTP_PORTS [36,80,81,82,83,84,85,86,87,88,89,90,311,383,555,591,593,631,801,808,818,901,972,1158,1220,1414,1533,1741,1830,1942,2231,2301,2381,2809,2980,3029,3037,3057,3128,3443,3702,4000,4343,4848,5000,5117,5250,5600,6080,6173,6988,7000,7001,7071,7144,7145,7510,7770,7777,7778,7779,8000,8008,8014,8028,8080,8081,8082,8085,8088,8090,8118,8123,8180,8181,8222,8243,8280,8300,8333,8344,8500,8509,8800,8888,8899,8983,9000,9060,9080,9090,9091,9111,9290,9443,9999,10000,11371,12601,13014,15489,29991,33300,34412,34443,34444,41080,44449,50000,50002,51423,53331,55252,55555,56712]
# List of ports you want to look for SHELLCODE on.
portvar SHELLCODE_PORTS !80
# List of ports you might see oracle attacks on
portvar ORACLE_PORTS 1024:
# List of ports you want to look for SSH connections on:
portvar SSH_PORTS 22
# List of ports you run ftp servers on
portvar FTP_PORTS [21,2100,3535]
# List of ports you run SIP servers on
portvar SIP_PORTS [5060,5061,5600]
# List of file data ports for file inspection
portvar FILE_DATA_PORTS [$HTTP_PORTS,110,143]
# List of GTP ports for GTP preprocessor
portvar GTP_PORTS [2123,2152,3386]
# other variables, these should not be modified
ipvar AIM_SERVERS [64.12.24.0/23,64.12.28.0/23,64.12.161.0/24,64.12.163.0/24,64.12.200.0/24,205.188.3.0/24,205.188.5.0/24,205.188.7.0/24,205.188.9.0/24,205.188.153.0/24,205.188.179.0/24,205.188.248.0/24]
# Path to your rules files (this can be a relative path)
# Note for Windows users: You are advised to make this an absolute path,
# such as: c:\snort\rules
var RULE_PATH /etc/snort/rules
var SO_RULE_PATH /etc/snort/so_rules
var PREPROC_RULE_PATH /etc/snort/preproc_rules
# If you are using reputation preprocessor set these
var WHITE_LIST_PATH /etc/snort/rules
var BLACK_LIST_PATH /etc/snort/rules
###################################################
# Step #2: Configure the decoder. For more information, see README.decode
###################################################
#config snort mode
config policy_mode:tap
# Stop generic decode events:
config disable_decode_alerts
# Stop Alerts on experimental TCP options
config disable_tcpopt_experimental_alerts
# Stop Alerts on obsolete TCP options
config disable_tcpopt_obsolete_alerts
# Stop Alerts on T/TCP alerts
config disable_tcpopt_ttcp_alerts
# Stop Alerts on all other TCPOption type events:
config disable_tcpopt_alerts
# Stop Alerts on invalid ip options
config disable_ipopt_alerts
# Alert if value in length field (IP, TCP, UDP) is greater th elength of the packet
# config enable_decode_oversized_alerts
# Same as above, but drop packet if in Inline mode (requires enable_decode_oversized_alerts)
# config enable_decode_oversized_drops
# Configure IP / TCP checksum mode
config checksum_mode: all
# Configure maximum number of flowbit references. For more information, see README.flowbits
# config flowbits_size: 64
# Configure ports to ignore
# config ignore_ports: tcp 21 6667:6671 1356
# config ignore_ports: udp 1:17 53
# Configure active response for non inline operation. For more information, see REAMDE.active
# config response: eth0 attempts 2
# Configure DAQ related options for inline operation. For more information, see README.daq
#
# config daq: <type>
# config daq_dir: <dir>
# config daq_mode: <mode>
# config daq_var: <var>
#
# <type> ::= pcap | afpacket | dump | nfq | ipq | ipfw
# <mode> ::= read-file | passive | inline
# <var> ::= arbitrary <name>=<value passed to DAQ
# <dir> ::= path as to where to look for DAQ module so's
# Configure specific UID and GID to run snort as after dropping privs. For more information see snort -h command line options
#
# config set_gid:
# config set_uid:
# Configure default snaplen. Snort defaults to MTU of in use interface. For more information see README
#
# config snaplen:
#
# Configure default bpf_file to use for filtering what traffic reaches snort. For more information see snort -h command line options (-F)
#
# config bpf_file:
#
# Configure default log directory for snort to log to. For more information see snort -h command line options (-l)
#
# config logdir:
###################################################
# Step #3: Configure the base detection engine. For more information, see README.decode
###################################################
# Configure PCRE match limitations
config pcre_match_limit: 3500
config pcre_match_limit_recursion: 1500
# Configure the detection engine See the Snort Manual, Configuring Snort - Includes - Config
config detection: search-method ac-split search-optimize max-pattern-len 20
# Configure the event queue. For more information, see README.event_queue
config event_queue: max_queue 8 log 5 order_events content_length
###################################################
## Configure GTP if it is to be used.
## For more information, see README.GTP
####################################################
# config enable_gtp
###################################################
# Per packet and rule latency enforcement
# For more information see README.ppm
###################################################
# Per Packet latency configuration
#config ppm: max-pkt-time 250, \
# fastpath-expensive-packets, \
# pkt-log
# Per Rule latency configuration
#config ppm: max-rule-time 200, \
# threshold 3, \
# suspend-expensive-rules, \
# suspend-timeout 20, \
# rule-log alert
###################################################
# Configure Perf Profiling for debugging
# For more information see README.PerfProfiling
###################################################
#config profile_rules: print all, sort avg_ticks
#config profile_preprocs: print all, sort avg_ticks
###################################################
# Configure protocol aware flushing
# For more information see README.stream5
###################################################
config paf_max: 16000
###################################################
# Step #4: Configure dynamic loaded libraries.
# For more information, see Snort Manual, Configuring Snort - Dynamic Modules
###################################################
# path to dynamic preprocessor libraries
dynamicpreprocessor directory /usr/local/lib/snort_dynamicpreprocessor/
# path to base preprocessor engine
dynamicengine /usr/local/lib/snort_dynamicengine/libsf_engine.so
# path to dynamic rules libraries
dynamicdetection directory /usr/local/lib/snort_dynamicrules
###################################################
# Step #5: Configure preprocessors
# For more information, see the Snort Manual, Configuring Snort - Preprocessors
###################################################
# GTP Control Channle Preprocessor. For more information, see README.GTP
# preprocessor gtp: ports { 2123 3386 2152 }
# Inline packet normalization. For more information, see README.normalize
# Does nothing in IDS mode
preprocessor normalize_ip4
preprocessor normalize_tcp: ips ecn stream
preprocessor normalize_icmp4
preprocessor normalize_ip6
preprocessor normalize_icmp6
# Target-based IP defragmentation. For more inforation, see README.frag3
preprocessor frag3_global: max_frags 65536
preprocessor frag3_engine: policy windows bind_to 10.4.0.0/24 detect_anomalies overlap_limit 10 min_fragment_length 100 timeout 60
# For Server zone
preprocessor frag3_engine: policy linux bind_to 10.4.1.0/24 detect_anomalies overlap_limit 10 min_fragment_length 100 timeout 60
# Target-Based stateful inspection/stream reassembly. For more inforation, see README.stream5
preprocessor stream5_global: track_tcp yes, \
track_udp yes, \
track_icmp no, \
max_tcp 262144, \
max_udp 131072, \
max_active_responses 2, \
min_response_seconds 5
preprocessor stream5_tcp: policy windows, detect_anomalies, require_3whs 180, \
overlap_limit 10, small_segments 3 bytes 150, timeout 180, \
ports client 21 22 23 25 42 53 70 79 109 110 111 113 119 135 136 137 139 143 \
161 445 513 514 587 593 691 1433 1521 1741 2100 3306 6070 6665 6666 6667 6668 6669 \
7000 8181 32770 32771 32772 32773 32774 32775 32776 32777 32778 32779, \
ports both 36 80 81 82 83 84 85 86 87 88 89 90 110 311 383 443 465 563 555 591 593 631 636 801 808 818 901 972 989 992 993 994 995 1158 1220 1414 1533 1741 1830 1942 2231 2301 2381 2809 2980 3029 3037 3057 3128 3443 3702 4000 4343 4848 5000 5117 5250 5600 6080 6173 6988 7907 7000 7001 7071 7144 7145 7510 7802 7770 7777 7778 7779 \
7801 7900 7901 7902 7903 7904 7905 7906 7908 7909 7910 7911 7912 7913 7914 7915 7916 \
7917 7918 7919 7920 8000 8008 8014 8028 8080 8081 8082 8085 8088 8090 8118 8123 8180 8181 8222 8243 8280 8300 8333 8344 8500 8509 8800 8888 8899 8983 9000 9060 9080 9090 9091 9111 9290 9443 9999 10000 11371 12601 13014 15489 29991 33300 34412 34443 34444 41080 44449 50000 50002 51423 53331 55252 55555 56712
preprocessor stream5_udp: timeout 180
# performance statistics. For more information, see the Snort Manual, Configuring Snort - Preprocessors - Performance Monitor
# preprocessor perfmonitor: time 300 file /var/snort/snort.stats pktcnt 10000
# HTTP normalization and anomaly detection. For more information, see README.http_inspect
preprocessor http_inspect: global iis_unicode_map unicode.map 1252 compress_depth 65535 decompress_depth 65535
preprocessor http_inspect_server: server default \
http_methods { GET POST PUT SEARCH MKCOL COPY MOVE LOCK UNLOCK NOTIFY POLL BCOPY BDELETE BMOVE LINK UNLINK OPTIONS HEAD DELETE TRACE TRACK CONNECT SOURCE SUBSCRIBE UNSUBSCRIBE PROPFIND PROPPATCH BPROPFIND BPROPPATCH RPC_CONNECT PROXY_SUCCESS BITS_POST CCM_POST SMS_POST RPC_IN_DATA RPC_OUT_DATA RPC_ECHO_DATA } \
chunk_length 500000 \
server_flow_depth 0 \
client_flow_depth 0 \
post_depth 65495 \
oversize_dir_length 500 \
max_header_length 750 \
max_headers 100 \
max_spaces 200 \
small_chunk_length { 10 5 } \
ports { 36 80 81 82 83 84 85 86 87 88 89 90 311 383 555 591 593 631 801 808 818 901 972 1158 1220 1414 1533 1741 1830 1942 2231 2301 2381 2809 2980 3029 3037 3057 3128 3443 3702 4000 4343 4848 5000 5117 5250 5600 6080 6173 6988 7000 7001 7071 7144 7145 7510 7770 7777 7778 7779 8000 8008 8014 8028 8080 8081 8082 8085 8088 8090 8118 8123 8180 8181 8222 8243 8280 8300 8333 8344 8500 8509 8800 8888 8899 8983 9000 9060 9080 9090 9091 9111 9290 9443 9999 10000 11371 12601 13014 15489 29991 33300 34412 34443 34444 41080 44449 50000 50002 51423 53331 55252 55555 56712 } \
non_rfc_char { 0x00 0x01 0x02 0x03 0x04 0x05 0x06 0x07 } \
enable_cookie \
extended_response_inspection \
inspect_gzip \
normalize_utf \
unlimited_decompress \
normalize_javascript \
apache_whitespace no \
ascii no \
bare_byte no \
directory no \
double_decode no \
iis_backslash no \
iis_delimiter no \
iis_unicode no \
multi_slash no \
utf_8 no \
u_encode yes \
webroot no
# ONC-RPC normalization and anomaly detection. For more information, see the Snort Manual, Configuring Snort - Preprocessors - RPC Decode
preprocessor rpc_decode: 111 32770 32771 32772 32773 32774 32775 32776 32777 32778 32779 no_alert_multiple_requests no_alert_large_fragments no_alert_incomplete
# Back Orifice detection.
preprocessor bo
# FTP / Telnet normalization and anomaly detection. For more information, see README.ftptelnet
preprocessor ftp_telnet: global inspection_type stateful encrypted_traffic no check_encrypted
preprocessor ftp_telnet_protocol: telnet \
ayt_attack_thresh 20 \
normalize ports { 23 } \
detect_anomalies
preprocessor ftp_telnet_protocol: ftp server default \
def_max_param_len 100 \
ports { 21 2100 3535 } \
telnet_cmds yes \
ignore_telnet_erase_cmds yes \
ftp_cmds { ABOR ACCT ADAT ALLO APPE AUTH CCC CDUP } \
ftp_cmds { CEL CLNT CMD CONF CWD DELE ENC EPRT } \
ftp_cmds { EPSV ESTA ESTP FEAT HELP LANG LIST LPRT } \
ftp_cmds { LPSV MACB MAIL MDTM MIC MKD MLSD MLST } \
ftp_cmds { MODE NLST NOOP OPTS PASS PASV PBSZ PORT } \
ftp_cmds { PROT PWD QUIT REIN REST RETR RMD RNFR } \
ftp_cmds { RNTO SDUP SITE SIZE SMNT STAT STOR STOU } \
ftp_cmds { STRU SYST TEST TYPE USER XCUP XCRC XCWD } \
ftp_cmds { XMAS XMD5 XMKD XPWD XRCP XRMD XRSQ XSEM } \
ftp_cmds { XSEN XSHA1 XSHA256 } \
alt_max_param_len 0 { ABOR CCC CDUP ESTA FEAT LPSV NOOP PASV PWD QUIT REIN STOU SYST XCUP XPWD } \
alt_max_param_len 200 { ALLO APPE CMD HELP NLST RETR RNFR STOR STOU XMKD } \
alt_max_param_len 256 { CWD RNTO } \
alt_max_param_len 400 { PORT } \
alt_max_param_len 512 { SIZE } \
chk_str_fmt { ACCT ADAT ALLO APPE AUTH CEL CLNT CMD } \
chk_str_fmt { CONF CWD DELE ENC EPRT EPSV ESTP HELP } \
chk_str_fmt { LANG LIST LPRT MACB MAIL MDTM MIC MKD } \
chk_str_fmt { MLSD MLST MODE NLST OPTS PASS PBSZ PORT } \
chk_str_fmt { PROT REST RETR RMD RNFR RNTO SDUP SITE } \
chk_str_fmt { SIZE SMNT STAT STOR STRU TEST TYPE USER } \
chk_str_fmt { XCRC XCWD XMAS XMD5 XMKD XRCP XRMD XRSQ } \
chk_str_fmt { XSEM XSEN XSHA1 XSHA256 } \
cmd_validity ALLO < int [ char R int ] > \
cmd_validity EPSV < [ { char 12 | char A char L char L } ] > \
cmd_validity MACB < string > \
cmd_validity MDTM < [ date nnnnnnnnnnnnnn[.n[n[n]]] ] string > \
cmd_validity MODE < char ASBCZ > \
cmd_validity PORT < host_port > \
cmd_validity PROT < char CSEP > \
cmd_validity STRU < char FRPO [ string ] > \
cmd_validity TYPE < { char AE [ char NTC ] | char I | char L [ number ] } >
preprocessor ftp_telnet_protocol: ftp client default \
max_resp_len 256 \
bounce yes \
ignore_telnet_erase_cmds yes \
telnet_cmds yes
# SMTP normalization and anomaly detection. For more information, see README.SMTP
preprocessor smtp: ports { 25 465 587 691 } \
inspection_type stateful \
b64_decode_depth 0 \
qp_decode_depth 0 \
bitenc_decode_depth 0 \
uu_decode_depth 0 \
log_mailfrom \
log_rcptto \
log_filename \
log_email_hdrs \
normalize cmds \
normalize_cmds { ATRN AUTH BDAT CHUNKING DATA DEBUG EHLO EMAL ESAM ESND ESOM ETRN EVFY } \
normalize_cmds { EXPN HELO HELP IDENT MAIL NOOP ONEX QUEU QUIT RCPT RSET SAML SEND SOML } \
normalize_cmds { STARTTLS TICK TIME TURN TURNME VERB VRFY X-ADAT X-DRCP X-ERCP X-EXCH50 } \
normalize_cmds { X-EXPS X-LINK2STATE XADR XAUTH XCIR XEXCH50 XGEN XLICENSE XQUE XSTA XTRN XUSR } \
max_command_line_len 512 \
max_header_line_len 1000 \
max_response_line_len 512 \
alt_max_command_line_len 260 { MAIL } \
alt_max_command_line_len 300 { RCPT } \
alt_max_command_line_len 500 { HELP HELO ETRN EHLO } \
alt_max_command_line_len 255 { EXPN VRFY ATRN SIZE BDAT DEBUG EMAL ESAM ESND ESOM EVFY IDENT NOOP RSET } \
alt_max_command_line_len 246 { SEND SAML SOML AUTH TURN ETRN DATA RSET QUIT ONEX QUEU STARTTLS TICK TIME TURNME VERB X-EXPS X-LINK2STATE XADR XAUTH XCIR XEXCH50 XGEN XLICENSE XQUE XSTA XTRN XUSR } \
valid_cmds { ATRN AUTH BDAT CHUNKING DATA DEBUG EHLO EMAL ESAM ESND ESOM ETRN EVFY } \
valid_cmds { EXPN HELO HELP IDENT MAIL NOOP ONEX QUEU QUIT RCPT RSET SAML SEND SOML } \
valid_cmds { STARTTLS TICK TIME TURN TURNME VERB VRFY X-ADAT X-DRCP X-ERCP X-EXCH50 } \
valid_cmds { X-EXPS X-LINK2STATE XADR XAUTH XCIR XEXCH50 XGEN XLICENSE XQUE XSTA XTRN XUSR } \
xlink2state { enabled }
# Portscan detection. For more information, see README.sfportscan
# preprocessor sfportscan: proto { all } memcap { 10000000 } sense_level { low }
# ARP spoof detection. For more information, see the Snort Manual - Configuring Snort - Preprocessors - ARP Spoof Preprocessor
# preprocessor arpspoof
# preprocessor arpspoof_detect_host: 192.168.40.1 f0:0f:00:f0:0f:00
# SSH anomaly detection. For more information, see README.ssh
preprocessor ssh: server_ports { 22 } \
autodetect \
max_client_bytes 19600 \
max_encrypted_packets 20 \
max_server_version_len 100 \
enable_respoverflow enable_ssh1crc32 \
enable_srvoverflow enable_protomismatch
# SMB / DCE-RPC normalization and anomaly detection. For more information, see README.dcerpc2
preprocessor dcerpc2: memcap 102400, events [co ]
preprocessor dcerpc2_server: default, policy WinXP, \
detect [smb [139,445], tcp 135, udp 135, rpc-over-http-server 593], \
autodetect [tcp 1025:, udp 1025:, rpc-over-http-server 1025:], \
smb_max_chain 3, smb_invalid_shares ["C$", "D$", "ADMIN$"]
# DNS anomaly detection. For more information, see README.dns
preprocessor dns: ports { 53 } enable_rdata_overflow
# SSL anomaly detection and traffic bypass. For more information, see README.ssl
preprocessor ssl: ports { 443 465 563 636 989 992 993 994 995 5061 7801 7802 7900 7901 7902 7903 7904 7905 7906 7907 7908 7909 7910 7911 7912 7913 7914 7915 7916 7917 7918 7919 7920 }, trustservers, noinspect_encrypted
# SDF sensitive data preprocessor. For more information see README.sensitive_data
preprocessor sensitive_data: alert_threshold 25
# SIP Session Initiation Protocol preprocessor. For more information see README.sip
preprocessor sip: max_sessions 40000, \
ports { 5060 5061 5600 }, \
methods { invite \
cancel \
ack \
bye \
register \
options \
refer \
subscribe \
update \
join \
info \
message \
notify \
benotify \
do \
qauth \
sprack \
publish \
service \
unsubscribe \
prack }, \
max_uri_len 512, \
max_call_id_len 80, \
max_requestName_len 20, \
max_from_len 256, \
max_to_len 256, \
max_via_len 1024, \
max_contact_len 512, \
max_content_len 2048
# IMAP preprocessor. For more information see README.imap
preprocessor imap: \
ports { 143 } \
b64_decode_depth 0 \
qp_decode_depth 0 \
bitenc_decode_depth 0 \
uu_decode_depth 0
# POP preprocessor. For more information see README.pop
preprocessor pop: \
ports { 110 } \
b64_decode_depth 0 \
qp_decode_depth 0 \
bitenc_decode_depth 0 \
uu_decode_depth 0
# Modbus preprocessor. For more information see README.modbus
preprocessor modbus: ports { 502 }
# DNP3 preprocessor. For more information see README.dnp3
preprocessor dnp3: ports { 20000 } \
memcap 262144 \
check_crc
# Reputation preprocessor. For more information see README.reputation
preprocessor reputation: \
memcap 500, \
priority whitelist, \
nested_ip inner, \
whitelist $WHITE_LIST_PATH/white_list.rules, \
blacklist $BLACK_LIST_PATH/black_list.rules
###################################################
# Step #6: Configure output plugins
# For more information, see Snort Manual, Configuring Snort - Output Modules
###################################################
# unified2
# Recommended for most installs
output unified2: filename merged.log, limit 128
# Additional configuration for specific types of installs
#output alert_unified2: filename snort.alert, limit 128, nostamp
#output log_unified2: filename snort.log, limit 128, nostamp
# syslog
output alert_syslog: LOG_AUTH LOG_ALERT
# pcap
output log_tcpdump: tcpdump.log
# metadata reference data. do not modify these lines
include classification.config
include reference.config
output alert_fast: snortalert.fast
###################################################
# Step #7: Customize your rule set
# For more information, see Snort Manual, Writing Snort Rules
#
# NOTE: All categories are enabled in this conf file
###################################################
# site specific rules
include $RULE_PATH/local.rules
include $RULE_PATH/app-detect.rules
include $RULE_PATH/attack-responses.rules
include $RULE_PATH/backdoor.rules
include $RULE_PATH/bad-traffic.rules
include $RULE_PATH/blacklist.rules
include $RULE_PATH/botnet-cnc.rules
include $RULE_PATH/browser-chrome.rules
include $RULE_PATH/browser-firefox.rules
include $RULE_PATH/browser-ie.rules
include $RULE_PATH/browser-other.rules
include $RULE_PATH/browser-plugins.rules
include $RULE_PATH/browser-webkit.rules
include $RULE_PATH/chat.rules
include $RULE_PATH/content-replace.rules
include $RULE_PATH/ddos.rules
include $RULE_PATH/dns.rules
include $RULE_PATH/dos.rules
include $RULE_PATH/experimental.rules
include $RULE_PATH/exploit-kit.rules
include $RULE_PATH/exploit.rules
include $RULE_PATH/file-executable.rules
include $RULE_PATH/file-flash.rules
include $RULE_PATH/file-identify.rules
include $RULE_PATH/file-image.rules
include $RULE_PATH/file-java.rules
include $RULE_PATH/file-multimedia.rules
include $RULE_PATH/file-office.rules
include $RULE_PATH/file-other.rules
include $RULE_PATH/file-pdf.rules
include $RULE_PATH/finger.rules
include $RULE_PATH/ftp.rules
include $RULE_PATH/icmp-info.rules
include $RULE_PATH/icmp.rules
include $RULE_PATH/imap.rules
include $RULE_PATH/indicator-compromise.rules
include $RULE_PATH/indicator-obfuscation.rules
include $RULE_PATH/indicator-scan.rules
include $RULE_PATH/indicator-shellcode.rules
include $RULE_PATH/info.rules
include $RULE_PATH/malware-backdoor.rules
include $RULE_PATH/malware-cnc.rules
include $RULE_PATH/malware-other.rules
include $RULE_PATH/malware-tools.rules
include $RULE_PATH/misc.rules
include $RULE_PATH/multimedia.rules
include $RULE_PATH/mysql.rules
include $RULE_PATH/netbios.rules
include $RULE_PATH/nntp.rules
include $RULE_PATH/oracle.rules
include $RULE_PATH/os-linux.rules
include $RULE_PATH/os-mobile.rules
include $RULE_PATH/os-other.rules
include $RULE_PATH/os-solaris.rules
include $RULE_PATH/os-windows.rules
include $RULE_PATH/other-ids.rules
include $RULE_PATH/p2p.rules
include $RULE_PATH/phishing-spam.rules
include $RULE_PATH/policy-multimedia.rules
include $RULE_PATH/policy-other.rules
include $RULE_PATH/policy.rules
include $RULE_PATH/policy-social.rules
include $RULE_PATH/policy-spam.rules
include $RULE_PATH/pop2.rules
include $RULE_PATH/pop3.rules
include $RULE_PATH/protocol-dns.rules
include $RULE_PATH/protocol-finger.rules
include $RULE_PATH/protocol-ftp.rules
include $RULE_PATH/protocol-icmp.rules
include $RULE_PATH/protocol-imap.rules
include $RULE_PATH/protocol-nntp.rules
include $RULE_PATH/protocol-pop.rules
include $RULE_PATH/protocol-rpc.rules
include $RULE_PATH/protocol-scada.rules
include $RULE_PATH/protocol-services.rules
include $RULE_PATH/protocol-snmp.rules
include $RULE_PATH/protocol-telnet.rules
include $RULE_PATH/protocol-tftp.rules
include $RULE_PATH/protocol-voip.rules
include $RULE_PATH/pua-adware.rules
include $RULE_PATH/pua-other.rules
include $RULE_PATH/pua-p2p.rules
include $RULE_PATH/pua-toolbars.rules
include $RULE_PATH/rpc.rules
include $RULE_PATH/rservices.rules
include $RULE_PATH/scada.rules
include $RULE_PATH/scan.rules
include $RULE_PATH/server-apache.rules
include $RULE_PATH/server-iis.rules
include $RULE_PATH/server-mail.rules
include $RULE_PATH/server-mssql.rules
include $RULE_PATH/server-mysql.rules
include $RULE_PATH/server-oracle.rules
include $RULE_PATH/server-other.rules
include $RULE_PATH/server-samba.rules
include $RULE_PATH/server-webapp.rules
include $RULE_PATH/shellcode.rules
include $RULE_PATH/smtp.rules
include $RULE_PATH/snmp.rules
include $RULE_PATH/specific-threats.rules
include $RULE_PATH/spyware-put.rules
include $RULE_PATH/sql.rules
include $RULE_PATH/telnet.rules
include $RULE_PATH/tftp.rules
include $RULE_PATH/virus.rules
include $RULE_PATH/voip.rules
include $RULE_PATH/web-activex.rules
include $RULE_PATH/web-attacks.rules
include $RULE_PATH/web-cgi.rules
include $RULE_PATH/web-client.rules
include $RULE_PATH/web-coldfusion.rules
include $RULE_PATH/web-frontpage.rules
include $RULE_PATH/web-iis.rules
include $RULE_PATH/web-misc.rules
include $RULE_PATH/web-php.rules
include $RULE_PATH/x11.rules
###################################################
# Step #8: Customize your preprocessor and decoder alerts
# For more information, see README.decoder_preproc_rules
###################################################
# decoder and preprocessor event rules
# include $PREPROC_RULE_PATH/preprocessor.rules
# include $PREPROC_RULE_PATH/decoder.rules
# include $PREPROC_RULE_PATH/sensitive-data.rules
###################################################
# Step #9: Customize your Shared Object Snort Rules
# For more information, see http://vrt-blog.snort.org/2009/01/using-vrt-certified-shared-object-rules.html
###################################################
# dynamic library rules
# include $SO_RULE_PATH/bad-traffic.rules
# include $SO_RULE_PATH/browser-ie.rules
# include $SO_RULE_PATH/chat.rules
# include $SO_RULE_PATH/dos.rules
# include $SO_RULE_PATH/exploit.rules
# include $SO_RULE_PATH/file-flash.rules
# include $SO_RULE_PATH/icmp.rules
# include $SO_RULE_PATH/imap.rules
# include $SO_RULE_PATH/misc.rules
# include $SO_RULE_PATH/multimedia.rules
# include $SO_RULE_PATH/netbios.rules
# include $SO_RULE_PATH/nntp.rules
# include $SO_RULE_PATH/p2p.rules
# include $SO_RULE_PATH/smtp.rules
# include $SO_RULE_PATH/snmp.rules
# include $SO_RULE_PATH/specific-threats.rules
# include $SO_RULE_PATH/web-activex.rules
# include $SO_RULE_PATH/web-client.rules
# include $SO_RULE_PATH/web-iis.rules
# include $SO_RULE_PATH/web-misc.rules
# Event thresholding or suppression commands. See threshold.conf
include threshold.conf
Reply all
Reply to author
Forward
0 new messages
