Intent to Prototype: Isolated Web Apps
Reilly Grant
Contact emails
rei...@chromium.org, pjmcl...@chromium.org
Explainer
https://github.com/reillyeon/isolated-web-apps/blob/main/README.md
Specification
Still at the explainer stage.
Summary
Isolated Web Apps extend Progressive Web App installation and Web Packaging to provide stronger protection against server compromise and other tampering. A small set of security-sensitive applications require this to migrate from Chrome Apps, Electron, or other web-adjacent solutions.
Rather than being hosted on live web servers and fetched over HTTPS, these applications are packaged into Web Bundles, signed by their developer, and distributed to end-users through one or more of the potential methods described in the explainer.
Blink component
UI>Browser>WebAppInstalls>Isolated (component request filed)
Motivation
Content Security Policy (CSP) provides strong protection against cross-site scripting (XSS) vulnerabilities. Transport Layer Security (TLS) and Subresource Integrity (SRI) provide protection against resources being tampered with in transit or when hosted on third-party servers. However, the threat model for some particularly security sensitive applications includes the main application server itself being compromised and serving malicious content. This goes beyond the protections that current policies can provide and requires exploring alternative ways that these applications could be distributed and validated.
TAG review
Not yet filed.
Risks
Interoperability and Compatibility
Gecko: No signal
WebKit: No signal
Web developers: No signals on this proposal but we’ve seen concerned developers looking for solutions in this space. See the explainer for details.
Other signals:
WebView application risks
Does this intent deprecate or change behavior of existing APIs, such that it has potentially high risk for Android WebView-based applications?
As this concept only applies to installed web applications it won’t be available in WebViews.
Debuggability
For the most part all the existing features to support debugability of PWAs and Web Bundles will apply. However, we are considering adding additional diagnostic messages to help developers understand when their application is misbehaving due to the stricter policies.
Is this feature fully tested by web-platform-tests?
No, web application installation is a //chrome concept which can’t be exercised by web-platform-tests. Browser test infrastructure is in isolated_app_test_utils.h.
Flag name
Developers can add an origin to --isolated-app-origins to enable isolation when installing a web app. Eventually this will support a real “developer mode” more similar to how Extensions development works.
Requires code in //chrome?
Yes, while much of the implementation will live in Blink and //content the web app installation infrastructure is implemented in //chrome.
Estimated milestones
No milestones specified
Link to entry on the Chrome Platform Status
https://chromestatus.com/feature/5146307550248960
This intent message was generated by Chrome Platform Status.
Alex Russell
Hyojin Song
Reilly Grant
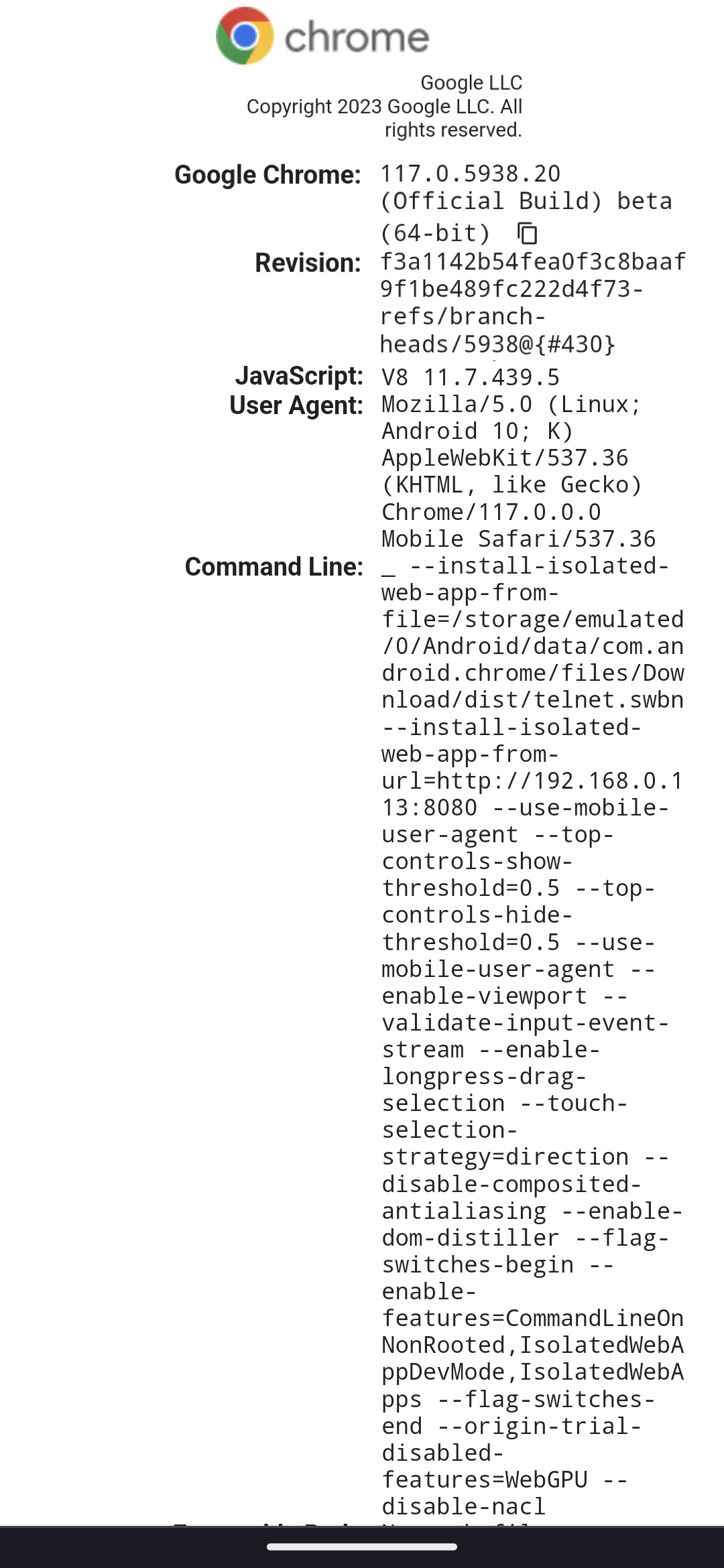
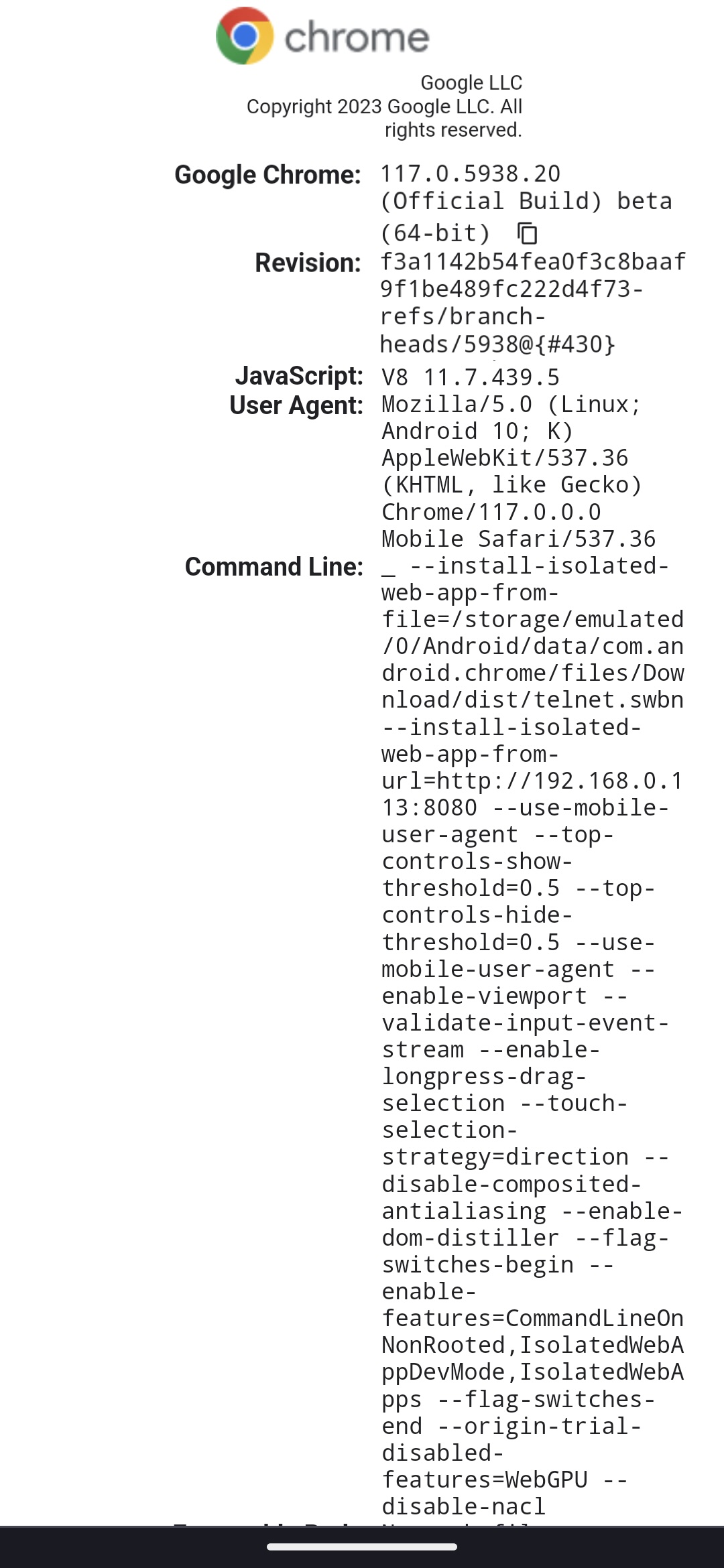
excellent work so far!we tested IWAs on android chromium 117.0.5x with the following issues:1) --install-isolated-web-app-from-url and --install-isolated-web-app-from-file did not work (https://bugs.chromium.org/p/chromium/issues/detail?id=1476843)2) direct-sockets api isn't available on android due to historical reasons mentioned here: https://chromestatus.com/feature/6398297361088512 . Can we get an update on what those original reasons were? (https://bugs.chromium.org/p/chromium/issues/detail?id=1476852)3) chrome://web-app-internals did not work on androidabout:version attached:
polyset
Daniel Herr
approach to how these apps are discovered and installed by users given the different user expectations on mobile vs. desktop.
polyset
Supporting Android is not on our near-term roadmap