oauth2 authentincation problem in 6.5 an 6.6
654 views
Skip to first unread message
Marcin Roman
Aug 1, 2022, 12:23:26 PM8/1/22
to CAS Community
Hi, I have a problem with oauth service after upgradeing from 6.4.x to 6.5.x or 6.6-RC5.
The service is defined as follows:
{
"@class" : "org.apereo.cas.support.oauth.services.OAuthRegisteredService",
"clientId": "praktyki",
"clientSecret": "***",
"bypassApprovalPrompt": true,
"serviceId" : "^https?://someservice*",
"name" : "praktyki",
"jsonFormat" : true,
"id" : 3,
"evaluationOrder" : 3,
"supportedGrantTypes" : [ "java.util.HashSet", [ "authorization_code", "password", "client_credentials", "refresh_token" ] ],
"supportedResponseTypes" : [ "java.util.HashSet", [ "code", "token" ] ],
"usernameAttributeProvider" : {
"@class" : "org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider",
"usernameAttribute" : "uidNumber"
},
"attributeReleasePolicy" : {
"@class" : "org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy",
"allowedAttributes" : [ "java.util.ArrayList", [ "uidNumber", "sn", "givenName", "displayName", "mail", "eduPersonAffiliation", "distinguishedName", "memberOf" ] ]
}
}
"@class" : "org.apereo.cas.support.oauth.services.OAuthRegisteredService",
"clientId": "praktyki",
"clientSecret": "***",
"bypassApprovalPrompt": true,
"serviceId" : "^https?://someservice*",
"name" : "praktyki",
"jsonFormat" : true,
"id" : 3,
"evaluationOrder" : 3,
"supportedGrantTypes" : [ "java.util.HashSet", [ "authorization_code", "password", "client_credentials", "refresh_token" ] ],
"supportedResponseTypes" : [ "java.util.HashSet", [ "code", "token" ] ],
"usernameAttributeProvider" : {
"@class" : "org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider",
"usernameAttribute" : "uidNumber"
},
"attributeReleasePolicy" : {
"@class" : "org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy",
"allowedAttributes" : [ "java.util.ArrayList", [ "uidNumber", "sn", "givenName", "displayName", "mail", "eduPersonAffiliation", "distinguishedName", "memberOf" ] ]
}
}
After successful login application tries to query for attributes of authenticated user, but then it seems that CAS cannot resolve username.
The following warning is logged:
yet the collection of attributes retrieved [[urn:oid:1.3.6.1.4.1.25178.1.2.9, credentialClass, credentialId, schacHomeOrganization, username]] do not contain any of those attributes. This is likely due
to misconfiguration and CAS will use [praktyki] as the final principal id>
The conversation is as follows:
1. Application redirects to cas:
2. CAS makes redirect to:
3. CAS makes yet another redirect to:
4. CAS redirects to:
5. CAS redirects back to the application:
6. Application makes accessToken requests, but cas responds with error 500:
GET /oauth2.0/accessToken?client_id=praktyki&client_secret=***&code=OC-13-aNSdcGkMW0eC93vYMI-0esZgpXws4AB2&grant_type=autho
rization_code&redirect_uri=https://praktyki.umcs.lublin.pl/authusos/token HTTP/1.1" 500
rization_code&redirect_uri=https://praktyki.umcs.lublin.pl/authusos/token HTTP/1.1" 500
Do I have sth misconfigured or is it some new bug?
The detailed log is below?
cas_1 | DEBUG [org.apereo.cas.support.oauth.util.OAuth20Utils] Response type: [code]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | DEBUG [org.apereo.cas.oidc.web.OidcAuthenticationAuthorizeSecurityLogic] Located OpenID Connect prompts from request as [[]]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Updating ticket [TransientSessionTicketImpl(super=TST-96005b5b-07d2-4036-b11e-c62aab27cf01, service=null, properties={ticketGrantingTicketId=TGT-1-********NzxO8k-login.umcs.pl, pac4jUserProfiles={CasOAuthClient=#CasProfile# | id: 2848 | attributes: { oauthClientId=praktyki, eduPersonAffiliation=[staff, employee], sAMAccountName=[rom3314], uidNumber=[2848], ,} | roles: [] | permissions: [] | isRemembered: false | clientName: CasOAuthClient | linkedId: null |}, bypass_approval_prompt=true})]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Fetched redis key [CAS_TICKET:TST-96005b5b-07d2-4036-b11e-c62aab27cf01:*] for ticket [TransientSessionTicketImpl(super=TST-96005b5b-07d2-4036-b11e-c62aab27cf01, service=null, properties={ticketGrantingTicketId=TGT-1-********NzxO8k-login.umcs.pl, pac4jUserProfiles={CasOAuthClient=#CasProfile# | id: 2848 | attributes: { oauthClientId=praktyki, eduPersonAffiliation=[staff, employee], sAMAccountName=[rom3314], uidNumber=[2848], ,} | roles: [] | permissions: [] | isRemembered: false | clientName: CasOAuthClient | linkedId: null |}, bypass_approval_prompt=true})]
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20DefaultCasAuthenticationBuilder] Created final principal [SimplePrincipal(id=2848, attributes={ eduPersonAffiliation=[staff, employee], , oauthClientId=[praktyki], sAMAccountName=[rom3314],, uidNumber=[2848]})] after filtering attributes based on [OAuthRegisteredService(super=BaseRegisteredService(serviceId=^https?://praktyki(-test)?.umcs.lublin.pl.*, name=praktyki, theme=null, locale=null, informationUrl=null, privacyUrl=null, responseType=null, id=3, description=null, expirationPolicy=DefaultRegisteredServiceExpirationPolicy(deleteWhenExpired=false, notifyWhenDeleted=false, notifyWhenExpired=false, expirationDate=null), ticketGrantingTicketExpirationPolicy=null, evaluationOrder=3, usernameAttributeProvider=PrincipalAttributeRegisteredServiceUsernameProvider(usernameAttribute=uidNumber), logoutType=BACK_CHANNEL, environments=[], attributeReleasePolicy=ReturnAllowedAttributeReleasePolicy(super=AbstractRegisteredServiceAttributeReleasePolicy(attributeFilter=null, principalAttributesRepository=DefaultPrincipalAttributesRepository(), consentPolicy=DefaultRegisteredServiceConsentPolicy(status=UNDEFINED, excludedAttributes=null, includeOnlyAttributes=null, order=0, excludedServices=null), authorizedToReleaseCredentialPassword=false, authorizedToReleaseProxyGrantingTicket=false, excludeDefaultAttributes=false, authorizedToReleaseAuthenticationAttributes=true, principalIdAttribute=null, order=0), allowedAttributes=[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName]), multifactorAuthenticationPolicy=DefaultRegisteredServiceMultifactorPolicy(multifactorAuthenticationProviders=[], failureMode=UNDEFINED, principalAttributeNameTrigger=null, principalAttributeValueToMatch=null, bypassEnabled=false, forceExecution=false, bypassTrustedDeviceEnabled=false, bypassPrincipalAttributeName=null, bypassPrincipalAttributeValue=null, script=null), publicKey=null, matchingStrategy=FullRegexRegisteredServiceMatchingStrategy(servicePattern=^https?://praktyki(-test)?.umcs.lublin.pl.*), logo=null, logoutUrl=null, accessStrategy=DefaultRegisteredServiceAccessStrategy(order=0, enabled=true, ssoEnabled=true, unauthorizedRedirectUrl=null, delegatedAuthenticationPolicy=DefaultRegisteredServiceDelegatedAuthenticationPolicy(allowedProviders=[], permitUndefined=true, exclusive=false, selectionStrategy=null), requireAllAttributes=true, requiredAttributes={}, rejectedAttributes={}, caseInsensitive=false), authenticationPolicy=DefaultRegisteredServiceAuthenticationPolicy(requiredAuthenticationHandlers=[], excludedAuthenticationHandlers=[], criteria=AnyAuthenticationHandlerRegisteredServiceAuthenticationPolicyCriteria(tryAll=false)), properties={}, contacts=[]), clientSecret=********, clientId=praktyki, bypassApprovalPrompt=true, generateRefreshToken=false, renewRefreshToken=false, jwtAccessToken=false, codeExpirationPolicy=null, accessTokenExpirationPolicy=null, refreshTokenExpirationPolicy=null, deviceTokenExpirationPolicy=null, supportedGrantTypes=[refresh_token, password, client_credentials, authorization_code], supportedResponseTypes=[code, token], userProfileViewType=null)]
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20DefaultCasAuthenticationBuilder] OAuth [state] is [], and [nonce] is []
cas_1 | TRACE [org.apereo.cas.services.RegisteredServiceAccessStrategyUtils] Checking access strategy for service [praktyki], requested by [2848] with attributes [{clientIpAddress=[10.1.0.20], bypassedMultifactorAuthenticationProviderId=[mfa-simple], bypassMultifactorAuthentication=[true], serverIpAddress=[172.24.0.4], userAgent=[Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.0.0 Safari/537.36], permissions=[], roles=[], scopes=[], state=[], nonce=[], client_id=[praktyki], eduPersonAffiliation=[staff, employee], , oauthClientId=[praktyki], sAMAccountName=[rom3314],, uidNumber=[2848]}].
cas_1 | TRACE [org.apereo.cas.services.util.RegisteredServiceAccessStrategyEvaluator] Skipping access strategy policy, since no attributes rules are defined
cas_1 | INFO [org.apereo.inspektr.audit.support.Slf4jLoggingAuditTrailManager] Audit trail record BEGIN
cas_1 | =============================================================
cas_1 | WHO: 2848
cas_1 | WHAT: {result=Service Access Granted, principal=SimplePrincipal(id=2848, attributes={ eduPersonAffiliation=[staff, employee], , oauthClientId=[praktyki], sAMAccountName=[rom3314],, uidNumber=[2848]}), service=praktyki, requiredAttributes={}}
cas_1 | ACTION: SERVICE_ACCESS_ENFORCEMENT_TRIGGERED
cas_1 | APPLICATION: CAS
cas_1 | WHEN: Mon Aug 01 18:11:34 CEST 2022
cas_1 | CLIENT IP ADDRESS: 10.1.0.20
cas_1 | SERVER IP ADDRESS: 172.24.0.4
cas_1 | =============================================================
cas_1 |
cas_1 |
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.DefaultOAuth20RequestParameterResolver] OAuth grant type is [NONE]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.DefaultOAuth20RequestParameterResolver] OAuth response type is [CODE]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.DefaultOAuth20RequestParameterResolver] OAuth response type is [NONE]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.endpoints.OAuth20AuthorizeEndpointController] Building authorization response for grant type [AUTHORIZATION_CODE] with scopes [[]] for client id [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.response.callback.OAuth20AuthorizationCodeAuthorizationResponseBuilder] Generated OAuth code: [OC-2-********mZEmEIsXRG1W7PITQ0ex]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Adding ticket [OC-2-********mZEmEIsXRG1W7PITQ0ex]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Updating ticket [TGT-1-********NzxO8k-login.umcs.pl]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Fetched redis key [CAS_TICKET:TGT-1-********NzxO8k-login.umcs.pl:rom3314] for ticket [TGT-1-********NzxO8k-login.umcs.pl]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.response.callback.OAuth20AuthorizationCodeAuthorizationResponseBuilder] Authorize request successful for client [praktyki] with redirect uri [https://praktyki.umcs.lublin.pl/authusos/callback]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.response.callback.OAuth20AuthorizationCodeAuthorizationResponseBuilder] Redirecting to URL [https://praktyki.umcs.lublin.pl/authusos/callback] with params [[code]] for clientId [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | INFO [org.apereo.inspektr.audit.support.Slf4jLoggingAuditTrailManager] Audit trail record BEGIN
cas_1 | =============================================================
cas_1 | WHO: 2848
cas_1 | WHAT: {code=OC-2-********mZEmEIsXRG1W7PITQ0ex}
cas_1 | ACTION: OAUTH2_CODE_RESPONSE_CREATED
cas_1 | APPLICATION: CAS
cas_1 | WHEN: Mon Aug 01 18:11:34 CEST 2022
cas_1 | CLIENT IP ADDRESS: 10.1.0.20
cas_1 | SERVER IP ADDRESS: 172.24.0.4
cas_1 | =============================================================
cas_1 |
cas_1 |
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request Body: [null]
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request does not specify a [TARGET] or request body is empty
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Service could not be extracted from request to enforce response headers
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request Body: [null]
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request does not specify a [TARGET] or request body is empty
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator] Authenticating credential [#UsernamePasswordCredentials# | username: praktyki | password: [PROTECTED] |]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | INFO [org.apereo.inspektr.audit.support.Slf4jLoggingAuditTrailManager] Audit trail record BEGIN
cas_1 | =============================================================
cas_1 | WHO: audit:unknown
cas_1 | WHAT: {result=Service Access Granted, requiredAttributes={}}
cas_1 | ACTION: SERVICE_ACCESS_ENFORCEMENT_TRIGGERED
cas_1 | APPLICATION: CAS
cas_1 | WHEN: Mon Aug 01 18:11:34 CEST 2022
cas_1 | CLIENT IP ADDRESS: 87.246.207.235
cas_1 | SERVER IP ADDRESS: 172.24.0.4
cas_1 | =============================================================
cas_1 |
cas_1 |
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator] Checking if the OAuth code issued contains code challenge
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Invoking principal resolver [PersonDirectoryPrincipalResolver]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Extracting credential id based on existing credential [UsernamePasswordCredential(username=praktyki, source=null, customFields={})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] No principal is currently resolved and available. Falling back onto using the identifier for the credential, that is [praktyki], for principal resolution
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Extracted principal id [praktyki]
cas_1 | DEBUG [org.apereo.cas.authentication.attribute.PrincipalAttributeRepositoryFetcher] Fetching person attributes for query [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], username=praktyki}]
cas_1 | DEBUG [org.apereo.services.persondir.support.AttributeBasedCacheKeyGenerator] Generated cache Map {9f089c5d8be0078af193b44cdbe38970a398554a925f664bae70646d7479cbe0f1e1c9829fa03ef39bddf2e7d67c63c4454f5dab72296a997ac42eac2a14c148=[praktyki]} from seed Map {credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], username=[praktyki]}
cas_1 | DEBUG [org.apereo.services.persondir.support.AttributeBasedCacheKeyGenerator] Generated cache key '-811107522|-811092114' for MethodInvocation='org.apereo.services.persondir.support.CachingPersonAttributeDaoImpl$PersonAttributeDaoMethodInvocation@22f2b39f'
cas_1 | DEBUG [org.apereo.services.persondir.support.CachingPersonAttributeDaoImpl] Retrieved query from cache for cachingAttributeRepository. key='getPeopleWithMultivaluedAttributes|-811107522|-811092114', results='[AttributeNamedPersonImpl[name=praktyki,attributes={urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]]'
cas_1 | DEBUG [org.apereo.services.persondir.support.CachingPersonAttributeDaoImpl.statistics] Cache Stats cachingAttributeRepository: queries=5, hits=1, misses=4
cas_1 | DEBUG [org.apereo.cas.authentication.attribute.PrincipalAttributeRepositoryFetcher] Retrieved person [AttributeNamedPersonImpl[name=praktyki,attributes={urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]] from attribute repositories for query [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], username=praktyki}]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Retrieved [5] attribute(s) from the repository
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [urn:oid:1.3.6.1.4.1.25178.1.2.9] with value(s) [[umcs.pl]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [credentialClass] with value(s) [[OAuth20ClientIdClientSecretCredential]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [credentialId] with value(s) [[praktyki]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [schacHomeOrganization] with value(s) [[umcs.pl]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [username] with value(s) [[praktyki]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Using principal attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] to determine principal id
cas_1 | WARN [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Principal resolution is set to resolve users via attribute(s) [sAMAccountName], and yet the collection of attributes retrieved [[urn:oid:1.3.6.1.4.1.25178.1.2.9, credentialClass, credentialId, schacHomeOrganization, username]] do not contain any of those attributes. This is likely due to misconfiguration and CAS will use [praktyki] as the final principal id
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Final resolved principal by [PersonDirectoryPrincipalResolver] is [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Resolved principal [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Invoking principal resolver [EchoingPrincipalResolver]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.EchoingPrincipalResolver] Echoing back the authenticated principal [Optional.empty]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Resolved principal [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Adding attributes [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]}] for the final principal
cas_1 | DEBUG [org.apereo.cas.authentication.CoreAuthenticationUtils] Merged attributes with the final result as [{credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.authentication.SurrogatePrincipalElectionStrategy] Calculating principal from principals [[SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.DefaultPrincipalElectionStrategy] Final principal constructed by the chain of resolvers is [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Initiating attributes release phase via [ReturnAllowedAttributeReleasePolicy] for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Using principal attribute repository [DefaultPrincipalAttributesRepository()] to retrieve attributes
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attributes retrieved from principal attribute repository for [praktyki] are [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Found principal attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Retrieving attribute definition store and attribute definitions...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finding requested attribute definitions [[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName, urn:oid:1.3.6.1.4.1.25178.1.2.9, credentialClass, credentialId, schacHomeOrganization, username]] based on available attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=sn, name=sn, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=sn, urn=urn:oid:2.5.4.4)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=givenName, name=givenName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=givenName, urn=urn:oid:2.5.4.42)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=displayName, name=displayName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=displayName, urn=urn:oid:2.16.840.1.113730.3.1.241)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=mail, name=mail, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=mail, urn=urn:oid:0.9.2342.19200300.100.1.3)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=eduPersonAffiliation, name=eduPersonAffiliation, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=eduPersonAffiliation, urn=urn:oid:1.3.6.1.4.1.5923.1.1.1.1)]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Resolved principal attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki] from attribute definition store
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Updating principal attributes repository cache for [praktyki] with [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Calling attribute policy [ReturnAllowedAttributeReleasePolicy] to process attributes for [praktyki]
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [uidNumber] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [distinguishedName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [memberOf] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [sAMAccountName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attribute policy [ReturnAllowedAttributeReleasePolicy] allows release of [{sAMAccountName=null, uidNumber=null, distinguishedName=null, memberOf=null}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attempting to merge policy attributes and default attributes
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Checking default attribute policy attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes for release are: [[]]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes found to be released are [{}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Adding policy attributes to the released set of attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finalizing attributes release phase for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Final collection of attributes allowed are: [{distinguishedName=null, memberOf=null, sAMAccountName=null, uidNumber=null}]
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Original principal attributes available for selection of username attribute [uidNumber] are [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]}].
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Located service [OAuthRegisteredService(super=BaseRegisteredService(serviceId=^https?://praktyki(-test)?.umcs.lublin.pl.*, name=praktyki, theme=null, locale=null, informationUrl=null, privacyUrl=null, responseType=null, id=3, description=null, expirationPolicy=DefaultRegisteredServiceExpirationPolicy(deleteWhenExpired=false, notifyWhenDeleted=false, notifyWhenExpired=false, expirationDate=null), ticketGrantingTicketExpirationPolicy=null, evaluationOrder=3, usernameAttributeProvider=PrincipalAttributeRegisteredServiceUsernameProvider(usernameAttribute=uidNumber), logoutType=BACK_CHANNEL, environments=[], attributeReleasePolicy=ReturnAllowedAttributeReleasePolicy(super=AbstractRegisteredServiceAttributeReleasePolicy(attributeFilter=null, principalAttributesRepository=DefaultPrincipalAttributesRepository(), consentPolicy=DefaultRegisteredServiceConsentPolicy(status=UNDEFINED, excludedAttributes=null, includeOnlyAttributes=null, order=0, excludedServices=null), authorizedToReleaseCredentialPassword=false, authorizedToReleaseProxyGrantingTicket=false, excludeDefaultAttributes=false, authorizedToReleaseAuthenticationAttributes=true, principalIdAttribute=null, order=0), allowedAttributes=[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName]), multifactorAuthenticationPolicy=DefaultRegisteredServiceMultifactorPolicy(multifactorAuthenticationProviders=[], failureMode=UNDEFINED, principalAttributeNameTrigger=null, principalAttributeValueToMatch=null, bypassEnabled=false, forceExecution=false, bypassTrustedDeviceEnabled=false, bypassPrincipalAttributeName=null, bypassPrincipalAttributeValue=null, script=null), publicKey=null, matchingStrategy=FullRegexRegisteredServiceMatchingStrategy(servicePattern=^https?://praktyki(-test)?.umcs.lublin.pl.*), logo=null, logoutUrl=null, accessStrategy=DefaultRegisteredServiceAccessStrategy(order=0, enabled=true, ssoEnabled=true, unauthorizedRedirectUrl=null, delegatedAuthenticationPolicy=DefaultRegisteredServiceDelegatedAuthenticationPolicy(allowedProviders=[], permitUndefined=true, exclusive=false, selectionStrategy=null), requireAllAttributes=true, requiredAttributes={}, rejectedAttributes={}, caseInsensitive=false), authenticationPolicy=DefaultRegisteredServiceAuthenticationPolicy(requiredAuthenticationHandlers=[], excludedAuthenticationHandlers=[], criteria=AnyAuthenticationHandlerRegisteredServiceAuthenticationPolicyCriteria(tryAll=false)), properties={}, contacts=[]), clientSecret=********, clientId=praktyki, bypassApprovalPrompt=true, generateRefreshToken=false, renewRefreshToken=false, jwtAccessToken=false, codeExpirationPolicy=null, accessTokenExpirationPolicy=null, refreshTokenExpirationPolicy=null, deviceTokenExpirationPolicy=null, supportedGrantTypes=[refresh_token, password, client_credentials, authorization_code], supportedResponseTypes=[code, token], userProfileViewType=null)] in the registry. Attempting to resolve attributes for [praktyki]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Initiating attributes release phase via [ReturnAllowedAttributeReleasePolicy] for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Using principal attribute repository [DefaultPrincipalAttributesRepository()] to retrieve attributes
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attributes retrieved from principal attribute repository for [praktyki] are [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Found principal attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Retrieving attribute definition store and attribute definitions...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finding requested attribute definitions [[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName, urn:oid:1.3.6.1.4.1.25178.1.2.9, credentialClass, credentialId, schacHomeOrganization, username]] based on available attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=sn, name=sn, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=sn, urn=urn:oid:2.5.4.4)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=givenName, name=givenName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=givenName, urn=urn:oid:2.5.4.42)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=displayName, name=displayName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=displayName, urn=urn:oid:2.16.840.1.113730.3.1.241)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=mail, name=mail, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=mail, urn=urn:oid:0.9.2342.19200300.100.1.3)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=eduPersonAffiliation, name=eduPersonAffiliation, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=eduPersonAffiliation, urn=urn:oid:1.3.6.1.4.1.5923.1.1.1.1)]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Resolved principal attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki] from attribute definition store
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Updating principal attributes repository cache for [praktyki] with [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Calling attribute policy [ReturnAllowedAttributeReleasePolicy] to process attributes for [praktyki]
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [uidNumber] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [distinguishedName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [memberOf] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [sAMAccountName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attribute policy [ReturnAllowedAttributeReleasePolicy] allows release of [{sAMAccountName=null, uidNumber=null, distinguishedName=null, memberOf=null}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attempting to merge policy attributes and default attributes
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Checking default attribute policy attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes for release are: [[]]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes found to be released are [{}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Adding policy attributes to the released set of attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finalizing attributes release phase for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Final collection of attributes allowed are: [{distinguishedName=null, memberOf=null, sAMAccountName=null, uidNumber=null}]
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Attributes resolved by the release policy available for selection of username attribute [uidNumber] are [{distinguishedName=null, memberOf=null, sAMAccountName=null, uidNumber=null}].
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Attribute release policy for registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*] contains an attribute for [uidNumber]
cas_1 | DEBUG [org.apereo.cas.web.FlowExecutionExceptionResolver] Ignoring the received exception [java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0] due to a type mismatch with handler [org.apereo.cas.support.oauth.web.endpoints.OAuth20AccessTokenEndpointController#handleGetRequest(HttpServletRequest, HttpServletResponse)]
cas_1 | ERROR [org.apache.catalina.core.ContainerBase.[Tomcat].[localhost].[/].[dispatcherServlet]] Servlet.service() for servlet [dispatcherServlet] in context with path [] threw exception [Request processing failed; nested exception is java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0] with root cause
cas_1 | java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0
cas_1 | at jdk.internal.util.Preconditions.outOfBounds(Unknown Source) ~[?:?]
cas_1 | at jdk.internal.util.Preconditions.outOfBoundsCheckIndex(Unknown Source) ~[?:?]
cas_1 | at jdk.internal.util.Preconditions.checkIndex(Unknown Source) ~[?:?]
cas_1 | at java.util.Objects.checkIndex(Unknown Source) ~[?:?]
cas_1 | at java.util.ArrayList.get(Unknown Source) ~[?:?]
cas_1 | at org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider.resolveUsernameInternal(PrincipalAttributeRegisteredServiceUsernameProvider.java:69) ~[cas-server-core-services-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apereo.cas.services.BaseRegisteredServiceUsernameAttributeProvider.resolveUsername(BaseRegisteredServiceUsernameAttributeProvider.java:47) ~[cas-server-core-services-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator.validate(OAuth20ClientIdClientSecretAuthenticator.java:91) ~[cas-server-support-oauth-core-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.pac4j.core.client.BaseClient.lambda$retrieveCredentials$0(BaseClient.java:75) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at java.util.Optional.ifPresent(Unknown Source) ~[?:?]
cas_1 | at org.pac4j.core.client.BaseClient.retrieveCredentials(BaseClient.java:72) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at org.pac4j.core.client.DirectClient.getCredentials(DirectClient.java:44) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at org.pac4j.core.engine.DefaultSecurityLogic.perform(DefaultSecurityLogic.java:107) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at org.pac4j.springframework.web.SecurityInterceptor.preHandle(SecurityInterceptor.java:118) ~[spring-webmvc-pac4j-6.0.3.jar!/:?]
cas_1 | at org.apereo.cas.support.oauth.web.OAuth20HandlerInterceptorAdapter.preHandle(OAuth20HandlerInterceptorAdapter.java:62) ~[cas-server-support-oauth-core-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apereo.cas.util.spring.RefreshableHandlerInterceptor.lambda$preHandle$0(RefreshableHandlerInterceptor.java:38) ~[cas-server-core-util-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.jooq.lambda.Unchecked.lambda$predicate$34(Unchecked.java:1506) ~[jool-0.9.14.jar!/:?]
cas_1 | at java.util.stream.MatchOps$1MatchSink.accept(Unknown Source) ~[?:?]
cas_1 | at java.util.AbstractList$RandomAccessSpliterator.tryAdvance(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.ReferencePipeline.forEachWithCancel(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.copyIntoWithCancel(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.copyInto(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.wrapAndCopyInto(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.evaluate(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.ReferencePipeline.allMatch(Unknown Source) ~[?:?]
cas_1 | at org.apereo.cas.util.spring.RefreshableHandlerInterceptor.preHandle(RefreshableHandlerInterceptor.java:38) ~[cas-server-core-util-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.springframework.web.servlet.HandlerExecutionChain.applyPreHandle(HandlerExecutionChain.java:148) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.DispatcherServlet.doDispatch(DispatcherServlet.java:1065) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.DispatcherServlet.doService(DispatcherServlet.java:963) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.FrameworkServlet.processRequest(FrameworkServlet.java:1006) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.FrameworkServlet.doGet(FrameworkServlet.java:898) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at javax.servlet.http.HttpServlet.service(HttpServlet.java:645) ~[javax.servlet-api-4.0.1.jar!/:4.0.1]
cas_1 | at org.springframework.web.servlet.FrameworkServlet.service(FrameworkServlet.java:883) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at javax.servlet.http.HttpServlet.service(HttpServlet.java:750) ~[javax.servlet-api-4.0.1.jar!/:4.0.1]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:227) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.servlet.resource.ResourceUrlEncodingFilter.doFilter(ResourceUrlEncodingFilter.java:67) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.AuthenticationCredentialsThreadLocalBinderClearingFilter.doFilter(AuthenticationCredentialsThreadLocalBinderClearingFilter.java:28) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.filters.RequestParameterPolicyEnforcementFilter.doFilter(RequestParameterPolicyEnforcementFilter.java:401) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.filters.ResponseHeadersEnforcementFilter.doFilter(ResponseHeadersEnforcementFilter.java:209) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.filters.AddResponseHeadersFilter.doFilter(AddResponseHeadersFilter.java:62) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:204) ~[spring-security-web-5.7.2.jar!/:5.7.2]
cas_1 | at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:183) ~[spring-security-web-5.7.2.jar!/:5.7.2]
cas_1 | at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:354) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:267) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.filter.RequestContextFilter.doFilterInternal(RequestContextFilter.java:100) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.filter.FormContentFilter.doFilterInternal(FormContentFilter.java:93) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.boot.actuate.metrics.web.servlet.WebMvcMetricsFilter.doFilterInternal(WebMvcMetricsFilter.java:96) ~[spring-boot-actuator-2.7.2.jar!/:2.7.2]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.logging.web.ThreadContextMDCServletFilter.doFilter(ThreadContextMDCServletFilter.java:104) ~[cas-server-core-logging-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.inspektr.common.web.ClientInfoThreadLocalFilter.doFilter(ClientInfoThreadLocalFilter.java:66) ~[inspektr-common-1.8.20.GA.jar!/:?]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.filter.CharacterEncodingFilter.doFilterInternal(CharacterEncodingFilter.java:201) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:197) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:97) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:541) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:135) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:92) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:78) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.valves.AbstractAccessLogValve.invoke(AbstractAccessLogValve.java:687) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.valves.RemoteIpValve.invoke(RemoteIpValve.java:769) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:360) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:399) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.coyote.AbstractProcessorLight.process(AbstractProcessorLight.java:65) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:890) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.net.NioEndpoint$SocketProcessor.doRun(NioEndpoint.java:1789) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.threads.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1191) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.threads.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:659) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at java.lang.Thread.run(Unknown Source) ~[?:?]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | DEBUG [org.apereo.cas.oidc.web.OidcAuthenticationAuthorizeSecurityLogic] Located OpenID Connect prompts from request as [[]]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Updating ticket [TransientSessionTicketImpl(super=TST-96005b5b-07d2-4036-b11e-c62aab27cf01, service=null, properties={ticketGrantingTicketId=TGT-1-********NzxO8k-login.umcs.pl, pac4jUserProfiles={CasOAuthClient=#CasProfile# | id: 2848 | attributes: { oauthClientId=praktyki, eduPersonAffiliation=[staff, employee], sAMAccountName=[rom3314], uidNumber=[2848], ,} | roles: [] | permissions: [] | isRemembered: false | clientName: CasOAuthClient | linkedId: null |}, bypass_approval_prompt=true})]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Fetched redis key [CAS_TICKET:TST-96005b5b-07d2-4036-b11e-c62aab27cf01:*] for ticket [TransientSessionTicketImpl(super=TST-96005b5b-07d2-4036-b11e-c62aab27cf01, service=null, properties={ticketGrantingTicketId=TGT-1-********NzxO8k-login.umcs.pl, pac4jUserProfiles={CasOAuthClient=#CasProfile# | id: 2848 | attributes: { oauthClientId=praktyki, eduPersonAffiliation=[staff, employee], sAMAccountName=[rom3314], uidNumber=[2848], ,} | roles: [] | permissions: [] | isRemembered: false | clientName: CasOAuthClient | linkedId: null |}, bypass_approval_prompt=true})]
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20DefaultCasAuthenticationBuilder] Created final principal [SimplePrincipal(id=2848, attributes={ eduPersonAffiliation=[staff, employee], , oauthClientId=[praktyki], sAMAccountName=[rom3314],, uidNumber=[2848]})] after filtering attributes based on [OAuthRegisteredService(super=BaseRegisteredService(serviceId=^https?://praktyki(-test)?.umcs.lublin.pl.*, name=praktyki, theme=null, locale=null, informationUrl=null, privacyUrl=null, responseType=null, id=3, description=null, expirationPolicy=DefaultRegisteredServiceExpirationPolicy(deleteWhenExpired=false, notifyWhenDeleted=false, notifyWhenExpired=false, expirationDate=null), ticketGrantingTicketExpirationPolicy=null, evaluationOrder=3, usernameAttributeProvider=PrincipalAttributeRegisteredServiceUsernameProvider(usernameAttribute=uidNumber), logoutType=BACK_CHANNEL, environments=[], attributeReleasePolicy=ReturnAllowedAttributeReleasePolicy(super=AbstractRegisteredServiceAttributeReleasePolicy(attributeFilter=null, principalAttributesRepository=DefaultPrincipalAttributesRepository(), consentPolicy=DefaultRegisteredServiceConsentPolicy(status=UNDEFINED, excludedAttributes=null, includeOnlyAttributes=null, order=0, excludedServices=null), authorizedToReleaseCredentialPassword=false, authorizedToReleaseProxyGrantingTicket=false, excludeDefaultAttributes=false, authorizedToReleaseAuthenticationAttributes=true, principalIdAttribute=null, order=0), allowedAttributes=[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName]), multifactorAuthenticationPolicy=DefaultRegisteredServiceMultifactorPolicy(multifactorAuthenticationProviders=[], failureMode=UNDEFINED, principalAttributeNameTrigger=null, principalAttributeValueToMatch=null, bypassEnabled=false, forceExecution=false, bypassTrustedDeviceEnabled=false, bypassPrincipalAttributeName=null, bypassPrincipalAttributeValue=null, script=null), publicKey=null, matchingStrategy=FullRegexRegisteredServiceMatchingStrategy(servicePattern=^https?://praktyki(-test)?.umcs.lublin.pl.*), logo=null, logoutUrl=null, accessStrategy=DefaultRegisteredServiceAccessStrategy(order=0, enabled=true, ssoEnabled=true, unauthorizedRedirectUrl=null, delegatedAuthenticationPolicy=DefaultRegisteredServiceDelegatedAuthenticationPolicy(allowedProviders=[], permitUndefined=true, exclusive=false, selectionStrategy=null), requireAllAttributes=true, requiredAttributes={}, rejectedAttributes={}, caseInsensitive=false), authenticationPolicy=DefaultRegisteredServiceAuthenticationPolicy(requiredAuthenticationHandlers=[], excludedAuthenticationHandlers=[], criteria=AnyAuthenticationHandlerRegisteredServiceAuthenticationPolicyCriteria(tryAll=false)), properties={}, contacts=[]), clientSecret=********, clientId=praktyki, bypassApprovalPrompt=true, generateRefreshToken=false, renewRefreshToken=false, jwtAccessToken=false, codeExpirationPolicy=null, accessTokenExpirationPolicy=null, refreshTokenExpirationPolicy=null, deviceTokenExpirationPolicy=null, supportedGrantTypes=[refresh_token, password, client_credentials, authorization_code], supportedResponseTypes=[code, token], userProfileViewType=null)]
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20DefaultCasAuthenticationBuilder] OAuth [state] is [], and [nonce] is []
cas_1 | TRACE [org.apereo.cas.services.RegisteredServiceAccessStrategyUtils] Checking access strategy for service [praktyki], requested by [2848] with attributes [{clientIpAddress=[10.1.0.20], bypassedMultifactorAuthenticationProviderId=[mfa-simple], bypassMultifactorAuthentication=[true], serverIpAddress=[172.24.0.4], userAgent=[Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.0.0 Safari/537.36], permissions=[], roles=[], scopes=[], state=[], nonce=[], client_id=[praktyki], eduPersonAffiliation=[staff, employee], , oauthClientId=[praktyki], sAMAccountName=[rom3314],, uidNumber=[2848]}].
cas_1 | TRACE [org.apereo.cas.services.util.RegisteredServiceAccessStrategyEvaluator] Skipping access strategy policy, since no attributes rules are defined
cas_1 | INFO [org.apereo.inspektr.audit.support.Slf4jLoggingAuditTrailManager] Audit trail record BEGIN
cas_1 | =============================================================
cas_1 | WHO: 2848
cas_1 | WHAT: {result=Service Access Granted, principal=SimplePrincipal(id=2848, attributes={ eduPersonAffiliation=[staff, employee], , oauthClientId=[praktyki], sAMAccountName=[rom3314],, uidNumber=[2848]}), service=praktyki, requiredAttributes={}}
cas_1 | ACTION: SERVICE_ACCESS_ENFORCEMENT_TRIGGERED
cas_1 | APPLICATION: CAS
cas_1 | WHEN: Mon Aug 01 18:11:34 CEST 2022
cas_1 | CLIENT IP ADDRESS: 10.1.0.20
cas_1 | SERVER IP ADDRESS: 172.24.0.4
cas_1 | =============================================================
cas_1 |
cas_1 |
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.DefaultOAuth20RequestParameterResolver] OAuth grant type is [NONE]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.DefaultOAuth20RequestParameterResolver] OAuth response type is [CODE]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.DefaultOAuth20RequestParameterResolver] OAuth response type is [NONE]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.endpoints.OAuth20AuthorizeEndpointController] Building authorization response for grant type [AUTHORIZATION_CODE] with scopes [[]] for client id [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.response.callback.OAuth20AuthorizationCodeAuthorizationResponseBuilder] Generated OAuth code: [OC-2-********mZEmEIsXRG1W7PITQ0ex]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Adding ticket [OC-2-********mZEmEIsXRG1W7PITQ0ex]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Updating ticket [TGT-1-********NzxO8k-login.umcs.pl]
cas_1 | DEBUG [org.apereo.cas.ticket.registry.RedisTicketRegistry] Fetched redis key [CAS_TICKET:TGT-1-********NzxO8k-login.umcs.pl:rom3314] for ticket [TGT-1-********NzxO8k-login.umcs.pl]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.response.callback.OAuth20AuthorizationCodeAuthorizationResponseBuilder] Authorize request successful for client [praktyki] with redirect uri [https://praktyki.umcs.lublin.pl/authusos/callback]
cas_1 | DEBUG [org.apereo.cas.support.oauth.web.response.callback.OAuth20AuthorizationCodeAuthorizationResponseBuilder] Redirecting to URL [https://praktyki.umcs.lublin.pl/authusos/callback] with params [[code]] for clientId [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | INFO [org.apereo.inspektr.audit.support.Slf4jLoggingAuditTrailManager] Audit trail record BEGIN
cas_1 | =============================================================
cas_1 | WHO: 2848
cas_1 | WHAT: {code=OC-2-********mZEmEIsXRG1W7PITQ0ex}
cas_1 | ACTION: OAUTH2_CODE_RESPONSE_CREATED
cas_1 | APPLICATION: CAS
cas_1 | WHEN: Mon Aug 01 18:11:34 CEST 2022
cas_1 | CLIENT IP ADDRESS: 10.1.0.20
cas_1 | SERVER IP ADDRESS: 172.24.0.4
cas_1 | =============================================================
cas_1 |
cas_1 |
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request Body: [null]
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request does not specify a [TARGET] or request body is empty
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Service could not be extracted from request to enforce response headers
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.services.web.support.RegisteredServiceResponseHeadersEnforcementFilter] Resolved registered service from request can not be located
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request Body: [null]
cas_1 | TRACE [org.apereo.cas.support.saml.authentication.principal.SamlServiceFactory] Request does not specify a [TARGET] or request body is empty
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator] Authenticating credential [#UsernamePasswordCredentials# | username: praktyki | password: [PROTECTED] |]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractServicesManager] No environments are assigned to service [wekan]
cas_1 | INFO [org.apereo.inspektr.audit.support.Slf4jLoggingAuditTrailManager] Audit trail record BEGIN
cas_1 | =============================================================
cas_1 | WHO: audit:unknown
cas_1 | WHAT: {result=Service Access Granted, requiredAttributes={}}
cas_1 | ACTION: SERVICE_ACCESS_ENFORCEMENT_TRIGGERED
cas_1 | APPLICATION: CAS
cas_1 | WHEN: Mon Aug 01 18:11:34 CEST 2022
cas_1 | CLIENT IP ADDRESS: 87.246.207.235
cas_1 | SERVER IP ADDRESS: 172.24.0.4
cas_1 | =============================================================
cas_1 |
cas_1 |
cas_1 | DEBUG [org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator] Checking if the OAuth code issued contains code challenge
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Invoking principal resolver [PersonDirectoryPrincipalResolver]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Extracting credential id based on existing credential [UsernamePasswordCredential(username=praktyki, source=null, customFields={})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] No principal is currently resolved and available. Falling back onto using the identifier for the credential, that is [praktyki], for principal resolution
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Extracted principal id [praktyki]
cas_1 | DEBUG [org.apereo.cas.authentication.attribute.PrincipalAttributeRepositoryFetcher] Fetching person attributes for query [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], username=praktyki}]
cas_1 | DEBUG [org.apereo.services.persondir.support.AttributeBasedCacheKeyGenerator] Generated cache Map {9f089c5d8be0078af193b44cdbe38970a398554a925f664bae70646d7479cbe0f1e1c9829fa03ef39bddf2e7d67c63c4454f5dab72296a997ac42eac2a14c148=[praktyki]} from seed Map {credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], username=[praktyki]}
cas_1 | DEBUG [org.apereo.services.persondir.support.AttributeBasedCacheKeyGenerator] Generated cache key '-811107522|-811092114' for MethodInvocation='org.apereo.services.persondir.support.CachingPersonAttributeDaoImpl$PersonAttributeDaoMethodInvocation@22f2b39f'
cas_1 | DEBUG [org.apereo.services.persondir.support.CachingPersonAttributeDaoImpl] Retrieved query from cache for cachingAttributeRepository. key='getPeopleWithMultivaluedAttributes|-811107522|-811092114', results='[AttributeNamedPersonImpl[name=praktyki,attributes={urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]]'
cas_1 | DEBUG [org.apereo.services.persondir.support.CachingPersonAttributeDaoImpl.statistics] Cache Stats cachingAttributeRepository: queries=5, hits=1, misses=4
cas_1 | DEBUG [org.apereo.cas.authentication.attribute.PrincipalAttributeRepositoryFetcher] Retrieved person [AttributeNamedPersonImpl[name=praktyki,attributes={urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]] from attribute repositories for query [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], username=praktyki}]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Retrieved [5] attribute(s) from the repository
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [urn:oid:1.3.6.1.4.1.25178.1.2.9] with value(s) [[umcs.pl]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [credentialClass] with value(s) [[OAuth20ClientIdClientSecretCredential]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [credentialId] with value(s) [[praktyki]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [schacHomeOrganization] with value(s) [[umcs.pl]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Found attribute [username] with value(s) [[praktyki]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Using principal attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] to determine principal id
cas_1 | WARN [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Principal resolution is set to resolve users via attribute(s) [sAMAccountName], and yet the collection of attributes retrieved [[urn:oid:1.3.6.1.4.1.25178.1.2.9, credentialClass, credentialId, schacHomeOrganization, username]] do not contain any of those attributes. This is likely due to misconfiguration and CAS will use [praktyki] as the final principal id
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.PersonDirectoryPrincipalResolver] Final resolved principal by [PersonDirectoryPrincipalResolver] is [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Resolved principal [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Invoking principal resolver [EchoingPrincipalResolver]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.EchoingPrincipalResolver] Echoing back the authenticated principal [Optional.empty]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Resolved principal [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.resolvers.ChainingPrincipalResolver] Adding attributes [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]}] for the final principal
cas_1 | DEBUG [org.apereo.cas.authentication.CoreAuthenticationUtils] Merged attributes with the final result as [{credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.authentication.SurrogatePrincipalElectionStrategy] Calculating principal from principals [[SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]]
cas_1 | DEBUG [org.apereo.cas.authentication.principal.DefaultPrincipalElectionStrategy] Final principal constructed by the chain of resolvers is [SimplePrincipal(id=praktyki, attributes={credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]})]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Initiating attributes release phase via [ReturnAllowedAttributeReleasePolicy] for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Using principal attribute repository [DefaultPrincipalAttributesRepository()] to retrieve attributes
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attributes retrieved from principal attribute repository for [praktyki] are [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Found principal attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Retrieving attribute definition store and attribute definitions...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finding requested attribute definitions [[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName, urn:oid:1.3.6.1.4.1.25178.1.2.9, credentialClass, credentialId, schacHomeOrganization, username]] based on available attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=sn, name=sn, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=sn, urn=urn:oid:2.5.4.4)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=givenName, name=givenName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=givenName, urn=urn:oid:2.5.4.42)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=displayName, name=displayName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=displayName, urn=urn:oid:2.16.840.1.113730.3.1.241)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=mail, name=mail, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=mail, urn=urn:oid:0.9.2342.19200300.100.1.3)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=eduPersonAffiliation, name=eduPersonAffiliation, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=eduPersonAffiliation, urn=urn:oid:1.3.6.1.4.1.5923.1.1.1.1)]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Resolved principal attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki] from attribute definition store
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Updating principal attributes repository cache for [praktyki] with [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Calling attribute policy [ReturnAllowedAttributeReleasePolicy] to process attributes for [praktyki]
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [uidNumber] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [distinguishedName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [memberOf] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [sAMAccountName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attribute policy [ReturnAllowedAttributeReleasePolicy] allows release of [{sAMAccountName=null, uidNumber=null, distinguishedName=null, memberOf=null}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attempting to merge policy attributes and default attributes
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Checking default attribute policy attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes for release are: [[]]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes found to be released are [{}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Adding policy attributes to the released set of attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finalizing attributes release phase for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Final collection of attributes allowed are: [{distinguishedName=null, memberOf=null, sAMAccountName=null, uidNumber=null}]
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Original principal attributes available for selection of username attribute [uidNumber] are [{credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], username=[praktyki]}].
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Located service [OAuthRegisteredService(super=BaseRegisteredService(serviceId=^https?://praktyki(-test)?.umcs.lublin.pl.*, name=praktyki, theme=null, locale=null, informationUrl=null, privacyUrl=null, responseType=null, id=3, description=null, expirationPolicy=DefaultRegisteredServiceExpirationPolicy(deleteWhenExpired=false, notifyWhenDeleted=false, notifyWhenExpired=false, expirationDate=null), ticketGrantingTicketExpirationPolicy=null, evaluationOrder=3, usernameAttributeProvider=PrincipalAttributeRegisteredServiceUsernameProvider(usernameAttribute=uidNumber), logoutType=BACK_CHANNEL, environments=[], attributeReleasePolicy=ReturnAllowedAttributeReleasePolicy(super=AbstractRegisteredServiceAttributeReleasePolicy(attributeFilter=null, principalAttributesRepository=DefaultPrincipalAttributesRepository(), consentPolicy=DefaultRegisteredServiceConsentPolicy(status=UNDEFINED, excludedAttributes=null, includeOnlyAttributes=null, order=0, excludedServices=null), authorizedToReleaseCredentialPassword=false, authorizedToReleaseProxyGrantingTicket=false, excludeDefaultAttributes=false, authorizedToReleaseAuthenticationAttributes=true, principalIdAttribute=null, order=0), allowedAttributes=[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName]), multifactorAuthenticationPolicy=DefaultRegisteredServiceMultifactorPolicy(multifactorAuthenticationProviders=[], failureMode=UNDEFINED, principalAttributeNameTrigger=null, principalAttributeValueToMatch=null, bypassEnabled=false, forceExecution=false, bypassTrustedDeviceEnabled=false, bypassPrincipalAttributeName=null, bypassPrincipalAttributeValue=null, script=null), publicKey=null, matchingStrategy=FullRegexRegisteredServiceMatchingStrategy(servicePattern=^https?://praktyki(-test)?.umcs.lublin.pl.*), logo=null, logoutUrl=null, accessStrategy=DefaultRegisteredServiceAccessStrategy(order=0, enabled=true, ssoEnabled=true, unauthorizedRedirectUrl=null, delegatedAuthenticationPolicy=DefaultRegisteredServiceDelegatedAuthenticationPolicy(allowedProviders=[], permitUndefined=true, exclusive=false, selectionStrategy=null), requireAllAttributes=true, requiredAttributes={}, rejectedAttributes={}, caseInsensitive=false), authenticationPolicy=DefaultRegisteredServiceAuthenticationPolicy(requiredAuthenticationHandlers=[], excludedAuthenticationHandlers=[], criteria=AnyAuthenticationHandlerRegisteredServiceAuthenticationPolicyCriteria(tryAll=false)), properties={}, contacts=[]), clientSecret=********, clientId=praktyki, bypassApprovalPrompt=true, generateRefreshToken=false, renewRefreshToken=false, jwtAccessToken=false, codeExpirationPolicy=null, accessTokenExpirationPolicy=null, refreshTokenExpirationPolicy=null, deviceTokenExpirationPolicy=null, supportedGrantTypes=[refresh_token, password, client_credentials, authorization_code], supportedResponseTypes=[code, token], userProfileViewType=null)] in the registry. Attempting to resolve attributes for [praktyki]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Initiating attributes release phase via [ReturnAllowedAttributeReleasePolicy] for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Using principal attribute repository [DefaultPrincipalAttributesRepository()] to retrieve attributes
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attributes retrieved from principal attribute repository for [praktyki] are [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Found principal attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Retrieving attribute definition store and attribute definitions...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finding requested attribute definitions [[uidNumber, sn, givenName, displayName, mail, eduPersonAffiliation, distinguishedName, memberOf, sAMAccountName, urn:oid:1.3.6.1.4.1.25178.1.2.9, credentialClass, credentialId, schacHomeOrganization, username]] based on available attributes [{urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=sn, name=sn, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=sn, urn=urn:oid:2.5.4.4)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=givenName, name=givenName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=givenName, urn=urn:oid:2.5.4.42)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=displayName, name=displayName, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=displayName, urn=urn:oid:2.16.840.1.113730.3.1.241)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=mail, name=mail, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=mail, urn=urn:oid:0.9.2342.19200300.100.1.3)]
cas_1 | WARN [org.apereo.cas.authentication.attribute.AttributeDefinitionStore] Unable to produce or determine attributes values for attribute definition [SamlIdPAttributeDefinition(super=DefaultAttributeDefinition(key=eduPersonAffiliation, name=eduPersonAffiliation, scoped=false, encrypted=false, attribute=null, patternFormat=null, script=null, canonicalizationMode=null), friendlyName=eduPersonAffiliation, urn=urn:oid:1.3.6.1.4.1.5923.1.1.1.1)]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Resolved principal attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}] for [praktyki] from attribute definition store
cas_1 | DEBUG [org.apereo.cas.authentication.principal.RegisteredServicePrincipalAttributesRepository] Using [praktyki], no caching/update takes place for [DefaultPrincipalAttributesRepository] to add attributes [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Updating principal attributes repository cache for [praktyki] with [{uidNumber=null, distinguishedName=null, memberOf=null, sAMAccountName=null, urn:oid:1.3.6.1.4.1.25178.1.2.9=[umcs.pl], credentialClass=[OAuth20ClientIdClientSecretCredential], credentialId=[praktyki], schacHomeOrganization=[umcs.pl], username=[praktyki]}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Calling attribute policy [ReturnAllowedAttributeReleasePolicy] to process attributes for [praktyki]
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [uidNumber] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [distinguishedName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [memberOf] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.ReturnAllowedAttributeReleasePolicy] Found attribute [sAMAccountName] in the list of allowed attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attribute policy [ReturnAllowedAttributeReleasePolicy] allows release of [{sAMAccountName=null, uidNumber=null, distinguishedName=null, memberOf=null}] for [praktyki]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Attempting to merge policy attributes and default attributes
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Checking default attribute policy attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes for release are: [[]]
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Default attributes found to be released are [{}]
cas_1 | TRACE [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Adding policy attributes to the released set of attributes
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Finalizing attributes release phase for principal [praktyki] accessing service [AbstractWebApplicationService(id=^https?://praktyki(-test)?.umcs.lublin.pl.*, originalUrl=^https?://praktyki(-test)?.umcs.lublin.pl.*, artifactId=null, principal=null, source=null, loggedOutAlready=false, format=XML, attributes={code=[OC-2-********mZEmEIsXRG1W7PITQ0ex], client_secret=********], redirect_uri=[https://praktyki.umcs.lublin.pl/authusos/token], grant_type=[authorization_code], client_id=[praktyki]})] defined by registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*]...
cas_1 | DEBUG [org.apereo.cas.services.AbstractRegisteredServiceAttributeReleasePolicy] Final collection of attributes allowed are: [{distinguishedName=null, memberOf=null, sAMAccountName=null, uidNumber=null}]
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Attributes resolved by the release policy available for selection of username attribute [uidNumber] are [{distinguishedName=null, memberOf=null, sAMAccountName=null, uidNumber=null}].
cas_1 | DEBUG [org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider] Attribute release policy for registered service [^https?://praktyki(-test)?.umcs.lublin.pl.*] contains an attribute for [uidNumber]
cas_1 | DEBUG [org.apereo.cas.web.FlowExecutionExceptionResolver] Ignoring the received exception [java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0] due to a type mismatch with handler [org.apereo.cas.support.oauth.web.endpoints.OAuth20AccessTokenEndpointController#handleGetRequest(HttpServletRequest, HttpServletResponse)]
cas_1 | ERROR [org.apache.catalina.core.ContainerBase.[Tomcat].[localhost].[/].[dispatcherServlet]] Servlet.service() for servlet [dispatcherServlet] in context with path [] threw exception [Request processing failed; nested exception is java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0] with root cause
cas_1 | java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0
cas_1 | at jdk.internal.util.Preconditions.outOfBounds(Unknown Source) ~[?:?]
cas_1 | at jdk.internal.util.Preconditions.outOfBoundsCheckIndex(Unknown Source) ~[?:?]
cas_1 | at jdk.internal.util.Preconditions.checkIndex(Unknown Source) ~[?:?]
cas_1 | at java.util.Objects.checkIndex(Unknown Source) ~[?:?]
cas_1 | at java.util.ArrayList.get(Unknown Source) ~[?:?]
cas_1 | at org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider.resolveUsernameInternal(PrincipalAttributeRegisteredServiceUsernameProvider.java:69) ~[cas-server-core-services-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apereo.cas.services.BaseRegisteredServiceUsernameAttributeProvider.resolveUsername(BaseRegisteredServiceUsernameAttributeProvider.java:47) ~[cas-server-core-services-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator.validate(OAuth20ClientIdClientSecretAuthenticator.java:91) ~[cas-server-support-oauth-core-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.pac4j.core.client.BaseClient.lambda$retrieveCredentials$0(BaseClient.java:75) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at java.util.Optional.ifPresent(Unknown Source) ~[?:?]
cas_1 | at org.pac4j.core.client.BaseClient.retrieveCredentials(BaseClient.java:72) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at org.pac4j.core.client.DirectClient.getCredentials(DirectClient.java:44) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at org.pac4j.core.engine.DefaultSecurityLogic.perform(DefaultSecurityLogic.java:107) ~[pac4j-core-5.4.3.jar!/:?]
cas_1 | at org.pac4j.springframework.web.SecurityInterceptor.preHandle(SecurityInterceptor.java:118) ~[spring-webmvc-pac4j-6.0.3.jar!/:?]
cas_1 | at org.apereo.cas.support.oauth.web.OAuth20HandlerInterceptorAdapter.preHandle(OAuth20HandlerInterceptorAdapter.java:62) ~[cas-server-support-oauth-core-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apereo.cas.util.spring.RefreshableHandlerInterceptor.lambda$preHandle$0(RefreshableHandlerInterceptor.java:38) ~[cas-server-core-util-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.jooq.lambda.Unchecked.lambda$predicate$34(Unchecked.java:1506) ~[jool-0.9.14.jar!/:?]
cas_1 | at java.util.stream.MatchOps$1MatchSink.accept(Unknown Source) ~[?:?]
cas_1 | at java.util.AbstractList$RandomAccessSpliterator.tryAdvance(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.ReferencePipeline.forEachWithCancel(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.copyIntoWithCancel(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.copyInto(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.wrapAndCopyInto(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.AbstractPipeline.evaluate(Unknown Source) ~[?:?]
cas_1 | at java.util.stream.ReferencePipeline.allMatch(Unknown Source) ~[?:?]
cas_1 | at org.apereo.cas.util.spring.RefreshableHandlerInterceptor.preHandle(RefreshableHandlerInterceptor.java:38) ~[cas-server-core-util-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.springframework.web.servlet.HandlerExecutionChain.applyPreHandle(HandlerExecutionChain.java:148) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.DispatcherServlet.doDispatch(DispatcherServlet.java:1065) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.DispatcherServlet.doService(DispatcherServlet.java:963) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.FrameworkServlet.processRequest(FrameworkServlet.java:1006) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.servlet.FrameworkServlet.doGet(FrameworkServlet.java:898) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at javax.servlet.http.HttpServlet.service(HttpServlet.java:645) ~[javax.servlet-api-4.0.1.jar!/:4.0.1]
cas_1 | at org.springframework.web.servlet.FrameworkServlet.service(FrameworkServlet.java:883) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at javax.servlet.http.HttpServlet.service(HttpServlet.java:750) ~[javax.servlet-api-4.0.1.jar!/:4.0.1]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:227) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.servlet.resource.ResourceUrlEncodingFilter.doFilter(ResourceUrlEncodingFilter.java:67) ~[spring-webmvc-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.AuthenticationCredentialsThreadLocalBinderClearingFilter.doFilter(AuthenticationCredentialsThreadLocalBinderClearingFilter.java:28) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.filters.RequestParameterPolicyEnforcementFilter.doFilter(RequestParameterPolicyEnforcementFilter.java:401) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.filters.ResponseHeadersEnforcementFilter.doFilter(ResponseHeadersEnforcementFilter.java:209) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.web.support.filters.AddResponseHeadersFilter.doFilter(AddResponseHeadersFilter.java:62) ~[cas-server-core-web-api-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:204) ~[spring-security-web-5.7.2.jar!/:5.7.2]
cas_1 | at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:183) ~[spring-security-web-5.7.2.jar!/:5.7.2]
cas_1 | at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:354) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:267) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.filter.RequestContextFilter.doFilterInternal(RequestContextFilter.java:100) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.filter.FormContentFilter.doFilterInternal(FormContentFilter.java:93) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.boot.actuate.metrics.web.servlet.WebMvcMetricsFilter.doFilterInternal(WebMvcMetricsFilter.java:96) ~[spring-boot-actuator-2.7.2.jar!/:2.7.2]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.cas.logging.web.ThreadContextMDCServletFilter.doFilter(ThreadContextMDCServletFilter.java:104) ~[cas-server-core-logging-6.6.0-RC5.jar!/:6.6.0-RC5]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apereo.inspektr.common.web.ClientInfoThreadLocalFilter.doFilter(ClientInfoThreadLocalFilter.java:66) ~[inspektr-common-1.8.20.GA.jar!/:?]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.springframework.web.filter.CharacterEncodingFilter.doFilterInternal(CharacterEncodingFilter.java:201) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117) ~[spring-web-5.3.22.jar!/:5.3.22]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:197) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:97) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:541) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:135) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:92) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:78) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.valves.AbstractAccessLogValve.invoke(AbstractAccessLogValve.java:687) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.valves.RemoteIpValve.invoke(RemoteIpValve.java:769) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:360) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:399) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.coyote.AbstractProcessorLight.process(AbstractProcessorLight.java:65) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:890) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.net.NioEndpoint$SocketProcessor.doRun(NioEndpoint.java:1789) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.threads.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1191) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.threads.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:659) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61) ~[tomcat-embed-core-9.0.65.jar!/:9.0.65]
cas_1 | at java.lang.Thread.run(Unknown Source) ~[?:?]
Mickaël
Aug 23, 2022, 10:12:48 AM8/23/22
to CAS Community, Marcin Roman
Hi,
The method is not a GET but a POST https://apereo.github.io/cas/6.3.x/installation/OAuth-OpenId-Authentication.html#endpoints
Cheers, Mickaël
Marcin Roman
Aug 23, 2022, 1:24:40 PM8/23/22
to CAS Community, Mickaël, Marcin Roman
Thank you, I have tried to make nginx rewrite GET into POST request, but it didn't worked.
location /oauth2.0/accessToken {
proxy_method POST;
proxy_set_header Content-Type application/x-www-form-urlencoded;
proxy_set_body $args;
}
Do you have an oauth2 client that can successfully authenticate with cas 6.5 or 6.6?
Marcin Roman
Nov 3, 2022, 2:36:51 PM11/3/22
to CAS Community, Marcin Roman, Mickaël
I have just tested my cas configuration using https://openidconnect.net/
The same problem.
The same problem.
{"body":"--- !<java.util.LinkedHashMap>\ntimestamp: \"2022-11-03T18:35:28.939+00:00\"\nstatus: 500\nerror: \"Internal Server Error\"\ntrace: \"java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0\\n\\t\\\n at java.base/jdk.internal.util.Preconditions.outOfBounds(Unknown Source)\\n\\tat java.base/jdk.internal.util.Preconditions.outOfBoundsCheckIndex(Unknown\\\n \\ Source)\\n\\tat java.base/jdk.internal.util.Preconditions.checkIndex(Unknown Source)\\n\\\n \\tat java.base/java.util.Objects.checkIndex(Unknown Source)\\n\\tat java.base/java.util.ArrayList.get(Unknown\\\n \\ Source)\\n\\tat org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider.resolveUsernameInternal(PrincipalAttributeRegisteredServiceUsernameProvider.java:69)\\n\\\n \\tat org.apereo.cas.services.BaseRegisteredServiceUsernameAttributeProvider.resolveUsername(BaseRegisteredServiceUsernameAttributeProvider.java:47)\\n\\\n \\tat org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator.validate(OAuth20ClientIdClientSecretAuthenticator.java:91)\\n\\\n \\tat org.pac4j.core.client.BaseClient.lambda$retrieveCredentials$0(BaseClient.java:75)\\n\\\n \\tat java.base/java.util.Optional.ifPresent(Unknown Source)\\n\\tat org.pac4j.core.client.BaseClient.retrieveCredentials(BaseClient.java:72)\\n\\\n \\tat org.pac4j.core.client.DirectClient.getCredentials(DirectClient.java:44)\\n\\t\\\n at org.pac4j.core.engine.DefaultSecurityLogic.perform(DefaultSecurityLogic.java:107)\\n\\\n \\tat org.pac4j.springframework.web.SecurityInterceptor.preHandle(SecurityInterceptor.java:118)\\n\\\n \\tat org.apereo.cas.support.oauth.web.OAuth20HandlerInterceptorAdapter.preHandle(OAuth20HandlerInterceptorAdapter.java:62)\\n\\\n \\tat org.apereo.cas.util.spring.RefreshableHandlerInterceptor.lambda$preHandle$0(RefreshableHandlerInterceptor.java:38)\\n\\\n \\tat org.jooq.lambda.Unchecked.lambda$predicate$34(Unchecked.java:1506)\\n\\tat java.base/java.util.stream.MatchOps$1MatchSink.accept(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.AbstractList$RandomAccessSpliterator.tryAdvance(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.stream.ReferencePipeline.forEachWithCancel(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.stream.AbstractPipeline.copyIntoWithCancel(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.stream.AbstractPipeline.copyInto(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.AbstractPipeline.wrapAndCopyInto(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.AbstractPipeline.evaluate(Unknown Source)\\n\\tat\\\n \\ java.base/java.util.stream.ReferencePipeline.allMatch(Unknown Source)\\n\\tat org.apereo.cas.util.spring.RefreshableHandlerInterceptor.preHandle(RefreshableHandlerInterceptor.java:38)\\n\\\n \\tat org.springframework.web.servlet.HandlerExecutionChain.applyPreHandle(HandlerExecutionChain.java:148)\\n\\\n \\tat org.springframework.web.servlet.DispatcherServlet.doDispatch(DispatcherServlet.java:1065)\\n\\\n \\tat org.springframework.web.servlet.DispatcherServlet.doService(DispatcherServlet.java:963)\\n\\\n \\tat org.springframework.web.servlet.FrameworkServlet.processRequest(FrameworkServlet.java:1006)\\n\\\n \\tat org.springframework.web.servlet.FrameworkServlet.doPost(FrameworkServlet.java:909)\\n\\\n \\tat javax.servlet.http.HttpServlet.service(HttpServlet.java:665)\\n\\tat org.springframework.web.servlet.FrameworkServlet.service(FrameworkServlet.java:883)\\n\\\n \\tat javax.servlet.http.HttpServlet.service(HttpServlet.java:750)\\n\\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:227)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.servlet.resource.ResourceUrlEncodingFilter.doFilter(ResourceUrlEncodingFilter.java:67)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.AuthenticationCredentialsThreadLocalBinderClearingFilter.doFilter(AuthenticationCredentialsThreadLocalBinderClearingFilter.java:28)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.filters.RequestParameterPolicyEnforcementFilter.doFilter(RequestParameterPolicyEnforcementFilter.java:401)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.filters.ResponseHeadersEnforcementFilter.doFilter(ResponseHeadersEnforcementFilter.java:209)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.filters.AddResponseHeadersFilter.doFilter(AddResponseHeadersFilter.java:62)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:214)\\n\\\n \\tat org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:186)\\n\\\n \\tat org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:354)\\n\\\n \\tat org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:267)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.filter.RequestContextFilter.doFilterInternal(RequestContextFilter.java:100)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.filter.FormContentFilter.doFilterInternal(FormContentFilter.java:93)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.boot.actuate.metrics.web.servlet.WebMvcMetricsFilter.doFilterInternal(WebMvcMetricsFilter.java:96)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.logging.web.ThreadContextMDCServletFilter.doFilter(ThreadContextMDCServletFilter.java:104)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.inspektr.common.web.ClientInfoThreadLocalFilter.doFilter(ClientInfoThreadLocalFilter.java:66)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.filter.CharacterEncodingFilter.doFilterInternal(CharacterEncodingFilter.java:201)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:197)\\n\\\n \\tat org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:97)\\n\\\n \\tat org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:541)\\n\\\n \\tat org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:135)\\n\\\n \\tat org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:92)\\n\\\n \\tat org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:78)\\n\\\n \\tat org.apache.catalina.valves.AbstractAccessLogValve.invoke(AbstractAccessLogValve.java:687)\\n\\\n \\tat org.apache.catalina.valves.RemoteIpValve.invoke(RemoteIpValve.java:769)\\n\\t\\\n at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:360)\\n\\\n \\tat org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:399)\\n\\\n \\tat org.apache.coyote.AbstractProcessorLight.process(AbstractProcessorLight.java:65)\\n\\\n \\tat org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:893)\\n\\\n \\tat org.apache.tomcat.util.net.NioEndpoint$SocketProcessor.doRun(NioEndpoint.java:1789)\\n\\\n \\tat org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49)\\n\\\n \\tat org.apache.tomcat.util.threads.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1191)\\n\\\n \\tat org.apache.tomcat.util.threads.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:659)\\n\\\n \\tat org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)\\n\\\n \\tat java.base/java.lang.Thread.run(Unknown Source)\\n\"\npath: \"/cas/oauth2.0/token\"\n","response":{"statusCode":500,"body":"--- !<java.util.LinkedHashMap>\ntimestamp: \"2022-11-03T18:35:28.939+00:00\"\nstatus: 500\nerror: \"Internal Server Error\"\ntrace: \"java.lang.IndexOutOfBoundsException: Index 0 out of bounds for length 0\\n\\t\\\n at java.base/jdk.internal.util.Preconditions.outOfBounds(Unknown Source)\\n\\tat java.base/jdk.internal.util.Preconditions.outOfBoundsCheckIndex(Unknown\\\n \\ Source)\\n\\tat java.base/jdk.internal.util.Preconditions.checkIndex(Unknown Source)\\n\\\n \\tat java.base/java.util.Objects.checkIndex(Unknown Source)\\n\\tat java.base/java.util.ArrayList.get(Unknown\\\n \\ Source)\\n\\tat org.apereo.cas.services.PrincipalAttributeRegisteredServiceUsernameProvider.resolveUsernameInternal(PrincipalAttributeRegisteredServiceUsernameProvider.java:69)\\n\\\n \\tat org.apereo.cas.services.BaseRegisteredServiceUsernameAttributeProvider.resolveUsername(BaseRegisteredServiceUsernameAttributeProvider.java:47)\\n\\\n \\tat org.apereo.cas.support.oauth.authenticator.OAuth20ClientIdClientSecretAuthenticator.validate(OAuth20ClientIdClientSecretAuthenticator.java:91)\\n\\\n \\tat org.pac4j.core.client.BaseClient.lambda$retrieveCredentials$0(BaseClient.java:75)\\n\\\n \\tat java.base/java.util.Optional.ifPresent(Unknown Source)\\n\\tat org.pac4j.core.client.BaseClient.retrieveCredentials(BaseClient.java:72)\\n\\\n \\tat org.pac4j.core.client.DirectClient.getCredentials(DirectClient.java:44)\\n\\t\\\n at org.pac4j.core.engine.DefaultSecurityLogic.perform(DefaultSecurityLogic.java:107)\\n\\\n \\tat org.pac4j.springframework.web.SecurityInterceptor.preHandle(SecurityInterceptor.java:118)\\n\\\n \\tat org.apereo.cas.support.oauth.web.OAuth20HandlerInterceptorAdapter.preHandle(OAuth20HandlerInterceptorAdapter.java:62)\\n\\\n \\tat org.apereo.cas.util.spring.RefreshableHandlerInterceptor.lambda$preHandle$0(RefreshableHandlerInterceptor.java:38)\\n\\\n \\tat org.jooq.lambda.Unchecked.lambda$predicate$34(Unchecked.java:1506)\\n\\tat java.base/java.util.stream.MatchOps$1MatchSink.accept(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.AbstractList$RandomAccessSpliterator.tryAdvance(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.stream.ReferencePipeline.forEachWithCancel(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.stream.AbstractPipeline.copyIntoWithCancel(Unknown\\\n \\ Source)\\n\\tat java.base/java.util.stream.AbstractPipeline.copyInto(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.AbstractPipeline.wrapAndCopyInto(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.MatchOps$MatchOp.evaluateSequential(Unknown Source)\\n\\\n \\tat java.base/java.util.stream.AbstractPipeline.evaluate(Unknown Source)\\n\\tat\\\n \\ java.base/java.util.stream.ReferencePipeline.allMatch(Unknown Source)\\n\\tat org.apereo.cas.util.spring.RefreshableHandlerInterceptor.preHandle(RefreshableHandlerInterceptor.java:38)\\n\\\n \\tat org.springframework.web.servlet.HandlerExecutionChain.applyPreHandle(HandlerExecutionChain.java:148)\\n\\\n \\tat org.springframework.web.servlet.DispatcherServlet.doDispatch(DispatcherServlet.java:1065)\\n\\\n \\tat org.springframework.web.servlet.DispatcherServlet.doService(DispatcherServlet.java:963)\\n\\\n \\tat org.springframework.web.servlet.FrameworkServlet.processRequest(FrameworkServlet.java:1006)\\n\\\n \\tat org.springframework.web.servlet.FrameworkServlet.doPost(FrameworkServlet.java:909)\\n\\\n \\tat javax.servlet.http.HttpServlet.service(HttpServlet.java:665)\\n\\tat org.springframework.web.servlet.FrameworkServlet.service(FrameworkServlet.java:883)\\n\\\n \\tat javax.servlet.http.HttpServlet.service(HttpServlet.java:750)\\n\\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:227)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.servlet.resource.ResourceUrlEncodingFilter.doFilter(ResourceUrlEncodingFilter.java:67)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.AuthenticationCredentialsThreadLocalBinderClearingFilter.doFilter(AuthenticationCredentialsThreadLocalBinderClearingFilter.java:28)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.filters.RequestParameterPolicyEnforcementFilter.doFilter(RequestParameterPolicyEnforcementFilter.java:401)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.filters.ResponseHeadersEnforcementFilter.doFilter(ResponseHeadersEnforcementFilter.java:209)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.web.support.filters.AddResponseHeadersFilter.doFilter(AddResponseHeadersFilter.java:62)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:214)\\n\\\n \\tat org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:186)\\n\\\n \\tat org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:354)\\n\\\n \\tat org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:267)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.filter.RequestContextFilter.doFilterInternal(RequestContextFilter.java:100)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.filter.FormContentFilter.doFilterInternal(FormContentFilter.java:93)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.boot.actuate.metrics.web.servlet.WebMvcMetricsFilter.doFilterInternal(WebMvcMetricsFilter.java:96)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.cas.logging.web.ThreadContextMDCServletFilter.doFilter(ThreadContextMDCServletFilter.java:104)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apereo.inspektr.common.web.ClientInfoThreadLocalFilter.doFilter(ClientInfoThreadLocalFilter.java:66)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.springframework.web.filter.CharacterEncodingFilter.doFilterInternal(CharacterEncodingFilter.java:201)\\n\\\n \\tat org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:117)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:189)\\n\\\n \\tat org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:162)\\n\\\n \\tat org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:197)\\n\\\n \\tat org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:97)\\n\\\n \\tat org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:541)\\n\\\n \\tat org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:135)\\n\\\n \\tat org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:92)\\n\\\n \\tat org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:78)\\n\\\n \\tat org.apache.catalina.valves.AbstractAccessLogValve.invoke(AbstractAccessLogValve.java:687)\\n\\\n \\tat org.apache.catalina.valves.RemoteIpValve.invoke(RemoteIpValve.java:769)\\n\\t\\\n at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:360)\\n\\\n \\tat org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:399)\\n\\\n \\tat org.apache.coyote.AbstractProcessorLight.process(AbstractProcessorLight.java:65)\\n\\\n \\tat org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:893)\\n\\\n \\tat org.apache.tomcat.util.net.NioEndpoint$SocketProcessor.doRun(NioEndpoint.java:1789)\\n\\\n \\tat org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49)\\n\\\n \\tat org.apache.tomcat.util.threads.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1191)\\n\\\n \\tat org.apache.tomcat.util.threads.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:659)\\n\\\n \\tat org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)\\n\\\n \\tat java.base/java.lang.Thread.run(Unknown Source)\\n\"\npath: \"/cas/oauth2.0/token\"\n","headers":{"server":"nginx","date":"Thu, 03 Nov 2022 18:35:28 GMT","content-type":"application/vnd.cas.services+yaml;charset=UTF-8","transfer-encoding":"chunked","connection":"close","requestid":"bcdd535e-4c61-4c36-8953-769750e814a2","cache-control":"no-cache, no-store, max-age=0, must-revalidate","pragma":"no-cache","expires":"0","strict-transport-security":"max-age=15768000 ; includeSubDomains","x-content-type-options":"nosniff","x-frame-options":"DENY","x-xss-protection":"1; mode=block","set-cookie":["org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en; Path=/; Secure; HttpOnly"],"www-authenticate":"Basic realm=\"authentication required\""},"request":{"uri":{"protocol":"https:","slashes":true,"auth":null,"host":"login.umcs.pl","port":443,"hostname":"login.umcs.pl","hash":null,"search":null,"query":null,"pathname":"/cas/oauth2.0/token","path":"/cas/oauth2.0/token","href":"https://login.umcs.pl/cas/oauth2.0/token"},"method":"POST","headers":{"content-type":"application/x-www-form-urlencoded","content-length":181}}},"decodedToken":"null"}
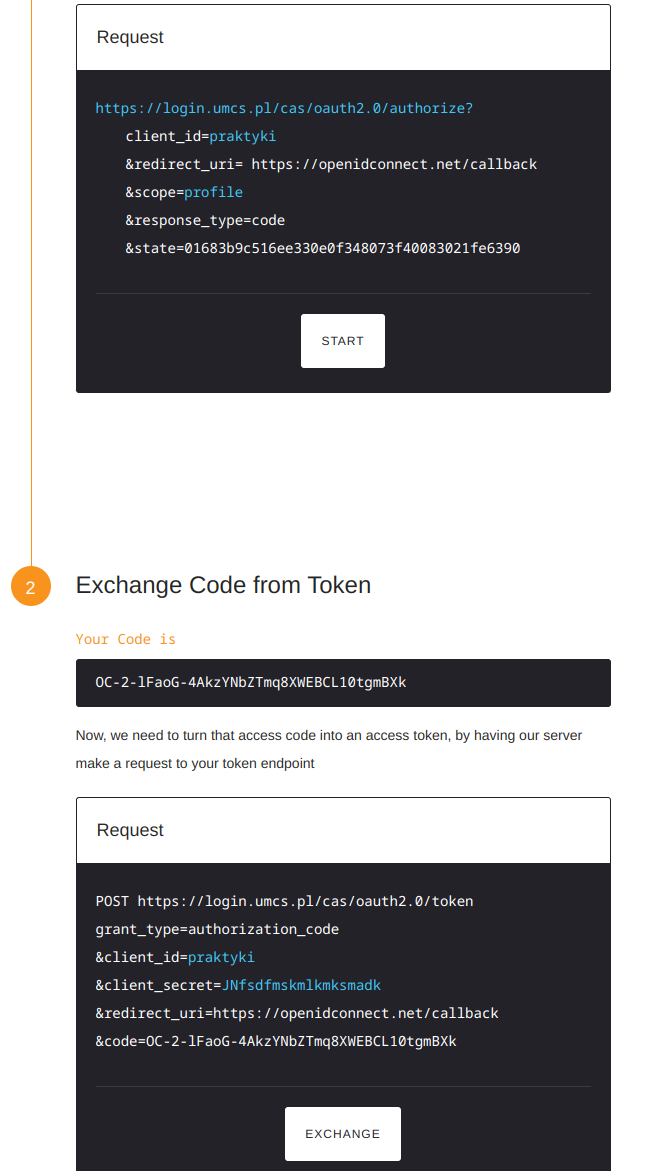
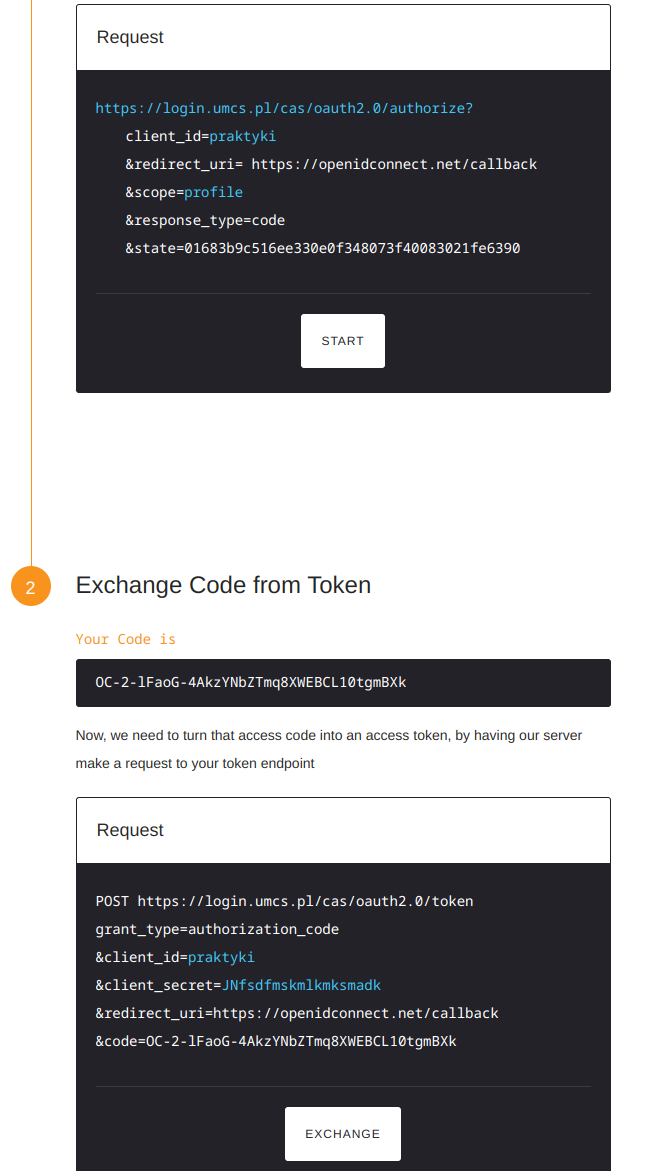
Reply all
Reply to author
Forward
0 new messages
